Key Points
- AirSnitch is a set of attacks that bypass Wi-Fi client isolation, allowing attackers to position themselves between devices and intercept or modify traffic
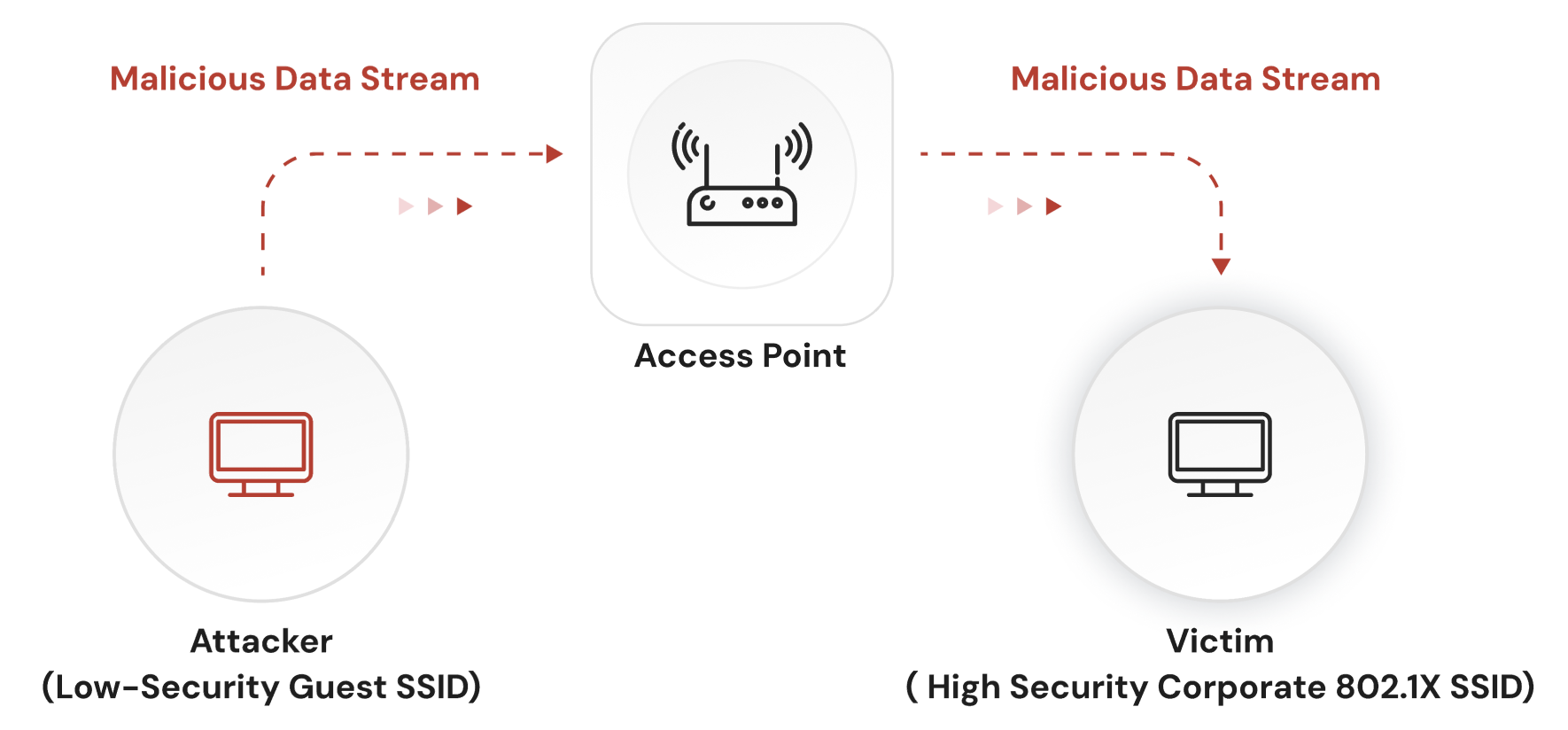
- Attackers can target devices across Open/Guest and Secure SSIDs when they share the same access point infrastructure or broadcast domain
- Once on the network, AirSnitch enables traffic interception, frame injection, and credential capture in weak authentication environments
- EAP-TLS, RadSec, and proper VLAN assignment each mitigate different parts of the attack chain and together form a resilient architecture
AirSnitch is a recently uncovered security vulnerability in Wi-Fi networks that allows devices on the same network to potentially attack each other. In research published at the Network and Distributed System Security (NDSS) Symposium on Feb. 25, 2026, a team of researchers reveal multiple ways to break client isolation, allowing attackers to gain access to other network devices.
Researchers from UC Riverside and KU Leuven tested 11 routers and networks from Cisco, Netgear, D-Link, ASUS, TP-Link, Ubiquiti, Tenda, and LANCOM, plus DD-WRT and OpenWrt firmware. Each one was vulnerable to at least one bypass technique.
The attacks, collectively named “AirSnitch,” don’t break WPA2 or WPA3 encryption. Instead, they exploit the inconsistent implementation of client isolation, which lacks a formal standard, and contains gaps at multiple layers of the network stack. The result is a documented set of techniques that let a connected attacker achieve a man-in-the-middle (MITM) position against other users on the same network.
This post covers how each version of the AirSnitch attack works, why enterprise environments carry the most exposure, and which authentication controls remain effective.
What Is AirSnitch?
AirSnitch is a set of three attacks that systematically bypass Wi-Fi client isolation. Client isolation is a feature that blocks direct communication between devices connected to the same Wi-Fi network. It is not defined in the IEEE 802.11 standard — vendors developed their own implementations independently, with no standards covering how isolation functions across all network layers.
AirSnitch has no CVE record, as the researchers felt that responsibility is distributed across vendors, and therefore not attributable to a single flaw in a single product. So, because the problem is architectural, no firmware patch addresses the issue comprehensively.
How AirSnitch Works
The three AirSnitch attacks each target a different layer of the network stack. An attacker only needs one of them to work.
AirSnitch Attack #1: GTK Abuse (Encryption Layer)
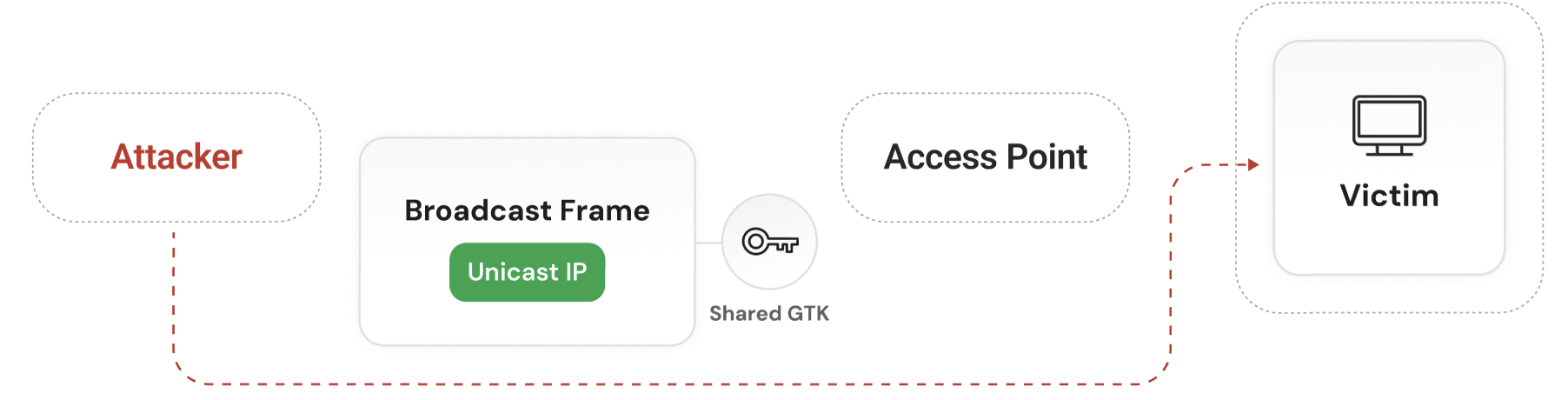
Every device on a WPA2 or WPA3 network is given the same Group Temporal Key (GTK), a shared encryption key used when the network sends traffic to multiple devices at once, such as an ARP request asking “who has this IP address?”.
Because every authenticated client receives the same key, an attacker who joins the network legitimately can use it to send data to other devices on the network that appear to come from the access point itself.
The attacker wraps a unicast IP payload inside a broadcast frame, encrypts it with the GTK, and transmits it using a spoofed AP MAC address. These frames are sent over the air and delivered directly to the target device, bypassing the AP’s forwarding path entirely, so client isolation controls are never applied.
The GTK Abuse version of AirSnitchworks against WPA2, WPA3, and even roaming consortiums like Passpoint and Hotspot 2.0. Many access points rotate GTKs on fixed intervals (hourly or daily) rather than on client disconnect. As a result, an attacker can continue injecting frames even after losing network access, until the GTK is rotated.
AirSnitch Attack #2: Gateway Bouncing (Routing Layer)
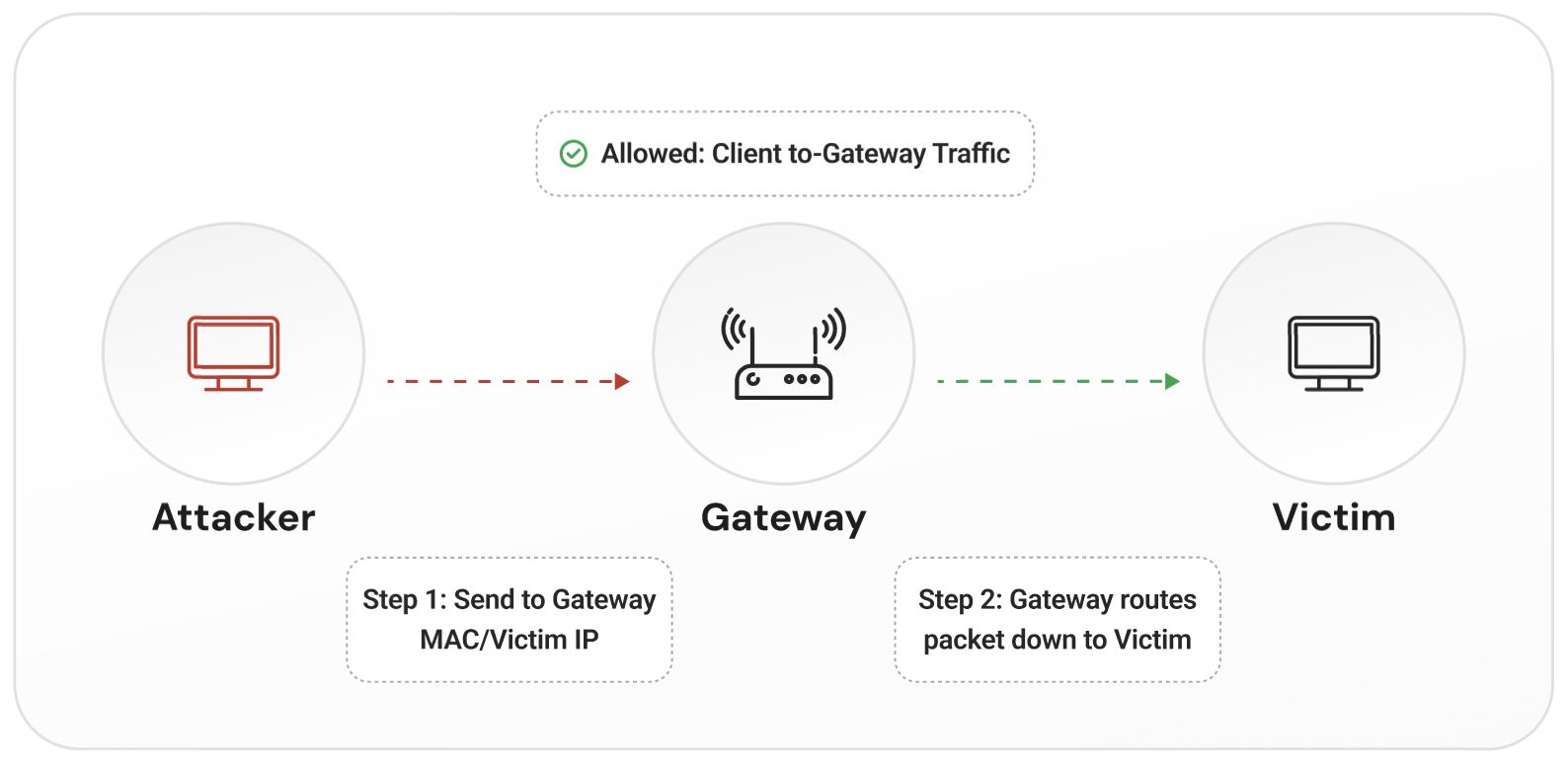
Many networks enforce client isolation at Layer 2 (the MAC layer), but not at Layer 3 (the IP routing layer) of the OSI model.
An AirSnitch attacker exploits this by sending a packet to the gateway (aka router) using the victim’s IP address as the destination and the gateway’s MAC address as the Layer 2 recipient. Gateway Bouncing appears as normal client-to-gateway traffic to the network infrastructure.
The gateway receives the packet, treats it as legitimate, and routes it to the victim. The AP only sees a client communicating with the gateway, which is allowed, instead of client-to-client traffic, which would be blocked.
This works because the network blocks direct device-to-device communication, but still allows all devices to communicate with the gateway. The gateway is just a relay used to reach the victim.
Importantly, in many enterprise deployments, routing happens at a central controller or upstream router. Once traffic reaches that point, the isolation enforced at the access point no longer applies. If the attacker and victim are on different VLANs, the gateway can enforce policy and block the traffic. But if they share the same network, the gateway will forward it.
AirSnitch Attack #3: Port Stealing (Switching Layer)
Access points maintain tables that map device MAC addresses to physical ports or radio associations. Port Stealing manipulates these tables.
The attacker spoofs the victim’s MAC address and associates on a different SSID (ideally an Open SSID, not one using 802.1X) that shares the same physical access point. The AP updates its table and now believes the victim’s MAC address is associated with the attacker’s session. Traffic intended for the victim is sent to the attacker instead.
In enterprise deployments, multiple access points can share the same wired network. Because these tables are updated dynamically, this behavior can extend across access points, not just within a single device. This allows the attacker to intercept traffic without needing to break encryption or bypass authentication.
Why Enterprise Networks Face Serious Risks From AirSnitch
The shared hardware problem: Running a guest SSID and a corporate SSID on the same physical access point is very common in enterprise and campus environments. AirSnitch’s port stealing attack works across SSIDs when they share the same AP hardware, so users on the guest network can target employees on the corporate SSID.
The RADIUS escalation chain: Many networks use PEAP/MSCHAPv2 for 802.1X authentication, which can expose passwords over the air to Evil Twin/Adversary in the Middle attacks. AirSnitch means Evil Twin networks aren’t even needed, as it allows an attacker on the same network to position themselves between the client and the AP.
“The biggest concern is for enterprise environments,” said lead researcher Xin’an Zhou, who conducted the AirSnitch research as a doctoral student at theUniversity of California, Riverside, in a press release. “Enterprise systems usually protect their networks using the most advanced encryption. So that means enterprises are seemingly relying on a fake sense of security.”
Authentication Security That Holds Against AirSnitch
In discussions with our global security teams, these are the security protocols SecureW2 recommends to defend against potential AirSnitch attacks.
- Prioritize EAP-TLS authentication
- Configure VLAN segmentation properly
- Implement RadSec for RADIUS servers
EAP-TLS Authentication
EAP-TLS uses mutual certificate authentication. The client presents a digital certificate the RADIUS server presents a digital certificate, and no password is transmitted during authentication.
An attacker who intercepts RADIUS traffic via port stealing captures a TLS handshake, not a credential, meaning there is nothing to brute force. The rogue AP and rogue RADIUS attack paths are also blocked: client devices verify the server certificate against a trusted certificate authority. A rogue server cannot present a valid certificate from your CA, so the connection is rejected.
EAP-TLS doesn’t prevent AirSnitch from establishing a MitM position, but more importantly, it means that position can’t capture anything relevant.
AirSnitch and RadSec
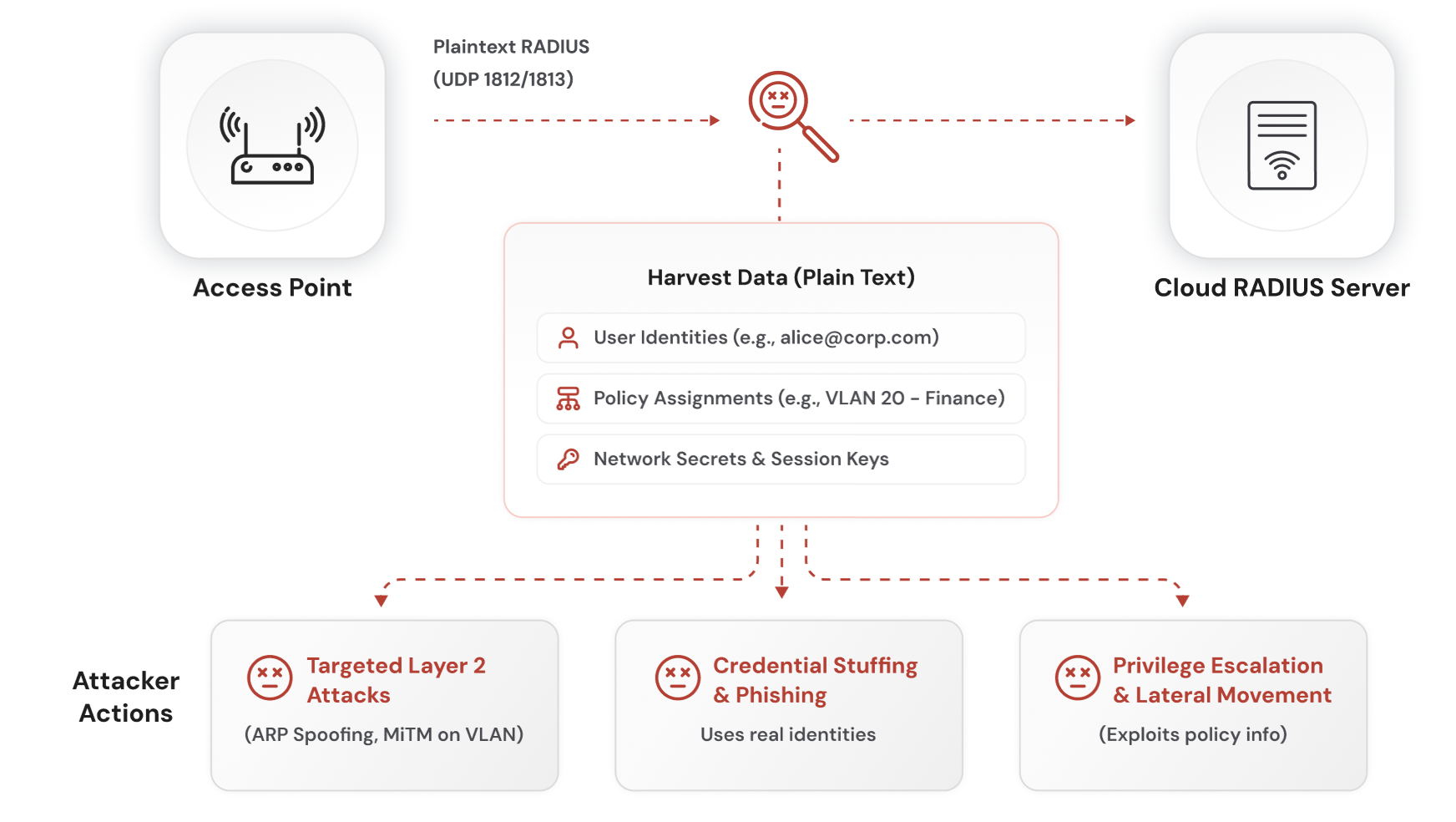
The RADIUS protocol was designed in 1991. Its standard security model encrypts only the password field in transit. The rest of the authentication exchange, including user identity, device attributes, and policy assignments, can be observed from captured packets.
AirSnitch does not directly expose RADIUS traffic in all deployments. However, if RADIUS communication is reachable or improperly segmented, this data becomes visible to an attacker in a position to capture it. Vulnerabilities include:
- User identities (work email addresses) can be used for credential stuffing or phishing attacks that appear legitimate.
- Policy assignments (e.g., VLAN 20 – Finance) reveal how the network is segmented, helping an attacker identify high-value targets.
- Authentication patterns can show when and how users connect, making it easier to time attacks or force reauthentication.
RadSec (RADIUS over TLS) protects these communications by encrypting the entire exchange between the access point and the RADIUS server. This prevents sensitive metadata from being exposed, even if traffic is intercepted.
AirSnitch and Per-User VLAN Assignment
Client isolation is enforced at the access point. AirSnitch shows that controls enforced at the AP are not reliable. VLAN assignment operates at a different layer. Each user is placed into a network segment defined at the switch or controller, not at the access point.
This segmentation is enforced in the wired infrastructure, which AirSnitch does not reach. As a result, users on different VLANs are in separate network domains. Traffic between them must pass through the gateway, where policy can be applied and access can be restricted.
A guest user assigned to a guest VLAN cannot access corporate resources, even after achieving a man-in-the-middle position on the wireless layer. The segmentation is enforced upstream of where AirSnitch operates.
Separate VLANs also use different broadcast domains and group keys. This limits the impact of GTK abuse to devices within the same VLAN and prevents cross-SSID exposure when networks are properly segmented.
What to Verify in Your Environment for AirSnitch Defense
For IT and network security teams, these are the specific items to check:
- EAP-TLS is active for all corporate SSIDs: Any segment still running PEAP/MSCHAPv2 allows credential material to be captured and cracked if authentication traffic is intercepted.
- Legacy authentication methods are fully disabled: Ensure PEAP/MSCHAPv2 and other password-based EAP methods are not available as fallback options on controllers or RADIUS policies.
- Guest, corporate, and IoT networks are segmented with VLANs: Devices on different trust levels should not share the same broadcast domain. If they do, AirSnitch can enable lateral movement within that network.
- VLAN enforcement happens at the switch or controller, not just the AP: Segmentation must be enforced in the wired infrastructure. AP-level isolation alone is not sufficient.
- RADIUS traffic is protected in transit: If RADIUS is sent over UDP with a shared secret, metadata and attributes may be exposed in packet captures. Consider RadSec to protect the full exchange.
- AP firmware and controller software are up to date: Some vendors have released mitigations for specific AirSnitch techniques, particularly around GTK handling and client isolation behavior.
- Client isolation behavior is understood and tested: Do not assume isolation works as expected. Validate how your network handles client-to-client, client-to-gateway, and cross-SSID traffic.
- Authentication activity is monitored for anomalies: Look for duplicate MAC associations, unexpected roaming events, and repeated reauthentication attempts, which may indicate port stealing or forced reconnects.
Protecting Against AirSnitch with SecureW2
The networks most exposed by AirSnitch are those that rely on password-based authentication. Protocols like PEAP/MSCHAPv2 allow an attacker to capture authentication exchanges and recover user credentials through offline cracking.
EAP-TLS removes this risk entirely. There is no password to capture, and no credential material that can be reused or cracked. With the SecureW2 platform you get a turnkey solution for EAP-TLS authentication, which can be set up in minutes.
The SecureW2 JoinNow Platform replaces passwords with digital certificates across Wi-Fi, VPN and web application access. JoinNow Cloud RADIUS delivers EAP-TLS authentication with RadSec support and per-user VLAN assignment built into RADIUS policy. Our Dynamic PKI issues and manages the certificates that replace passwords in your environment — for both managed devices via MDM auto-enrollment and unmanaged BYOD devices via JoinNow MultiOS self-service onboarding.
The architecture that can defeatAirSnitch is not new. Certificate-based authentication, encrypted RADIUS transport, and infrastructure-level segmentation have been the correct approach for years. AirSnitch makes the risk of skipping them visible.
Schedule a demo to see how SecureW2 closes the attack vectors AirSnitch exposed, or contact us to review your current configuration.