Network Access Control Service
Designed for Your Cloud
Enforce Cloud Network Access Control (Cloud NAC) for trusted identities with the SecureW2 agentless 802.1X platform.
Leverage policies from Okta, Entra ID, Jamf, CrowdStrike, and more to ensure only trusted, compliant users/devices access the network.
Certificates Are Critical for Cloud Network Access Control
Modern Cloud NAC depends on strong device and user identity. While password-based authentication leaves gaps in Network Access Control, digital certificates provide cryptographic proof of identity and device trust.
Our Certificate Lifecycle Management solution seamlessly extends your cloud identity environment. Create as many certificates as needed based on your identity infrastructure. Our managed cloud PKI enables certificates for multiple Cloud NAC authentication scenarios including:
- Network Authentication (Wi-Fi and VPN)
- Application Access
- Code Signing
- Smart Cards/Yubikeys
- Desktop Login
By integrating certificates with cloud identity providers, SecureW2 enables zero-trust Cloud NAC, ensuring only compliant users and devices receive network access.
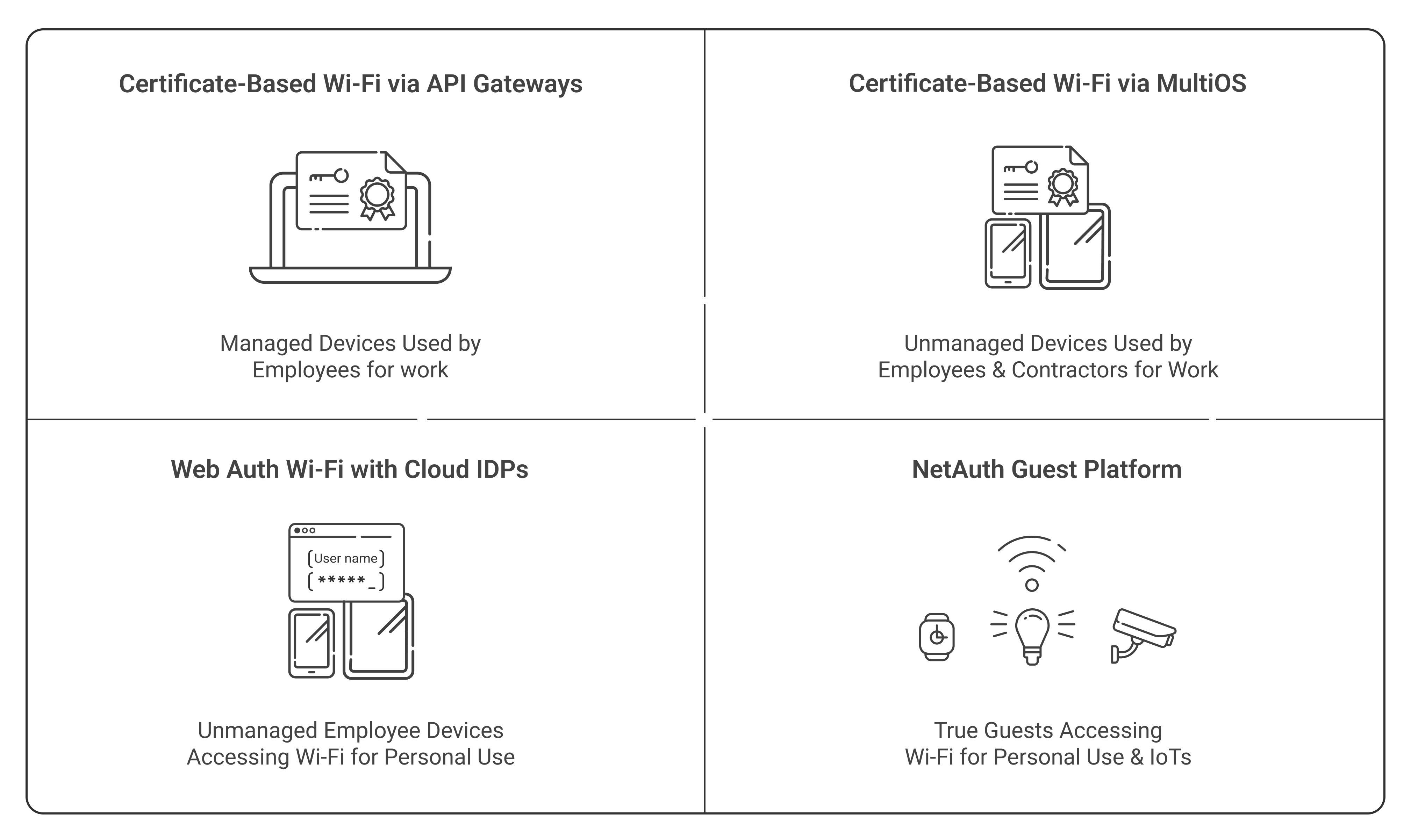
Cloud Network Access Control for All Devices and Identity Types
A true cloud-based NAC solution must support managed endpoints, BYOD devices, guests, and IoT systems. Certificate-based authentication provides the strongest level of Cloud NAC security ,but it’s not always feasible for all your devices. Guests or employees using personal devices on the enterprise network can’t adhere to the same security posture as other users.
Fortunately, our cloud NAC solution provides unique security controls for every type of user you might have.
- Certificate-Based Cloud Network Access Control: Easily issue certificates to endpoint devices to enforce Cloud NAC authentication.
- WebAuth Wi-Fi with Cloud IDPs: Secure Captive Portal for network access. Great for tying BYODs to Entra ID/Azure AD, Okta, Google, or OneLogin credentials.
- NetAuth Guest Platform: Allow guest users and IoTs access with our self-service login functionality or through access sponsored by your employees.
- MAC-Based Authentication (MAB) for IoT & Legacy Devices: Enforce Cloud NAC policies for devices that cannot support 802.1X authentication by leveraging MAC address filtering, dynamic VLAN segmentation, and policy-based access controls.
What Real Customers Have to Say About SecureW2
At SecureW2, we laser-focus on making products and services that customers love. But don’t take our word for it, check out what some of our customers are saying:
Zero Trust Cloud NAC Built for Your Environment
SecureW2 Zero Trust NAC architecture continuously validates user and device identity using certificate-based authentication that evaluates real-time security signals from identity providers, MDMs, and endpoint security platforms (EDR/XDR). This enables dynamic runtime policy enforcement within our Cloud NAC platform, eliminating the need for traditional appliance-based NAC infrastructure.
Enforce Cloud Network Access Control Policies in Real-Time
Cloud NAC must enforce dynamic policies at the moment of authentication. SecureW2 integrates directly with Entra ID, Okta, Jamf, Intune, and other identity and security sources to apply access decisions instantly.
Eliminate frustrating password complexity and reset employee policies on corporate networks and devices while significantly improving authentication security for Wi-Fi, VPN, Single-Sign-On, and more.
- Tie user/device identity to every connection for detailed tracking and segmentation.
- Avoid unauthorized users/devices from accessing the network.
- Divide your network into smaller VLAN segments to prevent attacks on the system surface.
- Lookup user/device status in all significant Cloud Identity Providers to authenticate them in real time.
- Auto-revoke certificates when lookups fail, ensuring continuous enforcement in your Cloud NAC environment.
Certificate Lifecycle Management for Cloud NAC
With SecureW2, using digital certificates for Network Access Control is easier than ever. Our Certificate Lifecycle Management solution extends your cloud environment, automating the certificate lifecycle based on real-time data from your Cloud Identity. Now, you can use all your Entra ID/Azure, Okta, Jamf, or Intune policies to automate certificate management.
- Search for users/devices and easily view all their digital certificate lifecycles and authentication events in one place for easy troubleshooting and management.
- Offer protection for Private Keys using FIPS140-2 Level 3+ standard HSM's.
- Integrate with ease to nearly every device management system or with BYODs/unmanaged devices.
- Automate certificate enrollment and revocation to all your managed devices through our APIs.
- Total cost of ownership (TCO) is less than a third of comparable on-premise PKI solutions.
Auto-Enroll Certificates to Managed Devices
Certificate distribution and management for all your managed devices with no need for complex infrastructure changes.
- Zero-touch certificate distribution and renewal via extensive APIs including ACME, SCEP, JSON, WSTEP, EST, and more.
- Auto-revoke certificates through your MDM when a user/device leaves the organization.
- Proven integration with all major MDMs including Jamf, Workspace One, Soti, Mosyle, MobileIron, Meraki, and many more.
All it takes is two easy steps:
- Step 1: Configure your MDM platform with our PKI services.
- Step 2: Send out configuration profiles directing managed devices to auto-enroll for a certificate and self-service for 802.1X.
Secure BYOD Enrollment with Cloud-Based Network Access Control
BYODs and unmanaged devices don’t have to be complex or time-consuming to configure for secure network access. Our cloud NAC solution:
- Provides passwordless enrollment for robust authentication.
- Prevents unauthorized users and devices from accessing confidential/unauthorized data.
- Stops Over-the-air cyber attacks from intercepting sensitive information.
- Integrates natively with major identity providers, including Entra ID, Okta, and Google.
Cloud Network Access Control (Cloud NAC) FAQS
How Do PKI and RADIUS Enable Cloud Network Access Control?
Network access control (NAC) combines software, rules, and policies to establish controlled access in restricted environments. In a Cloud NAC architecture, PKI and RADIUS work together to enforce authentication and authorization without requiring endpoint agents.
The SecureW2 network security solution leverages RADIUS and PKI technology to control access and authorization of your network without requiring an agent to stay persistently active on the device. Our PKI integrates with your identity, device management, and security infrastructure so you can be confident that only trusted users and devices are issued certificates.
Since certificates are non-exportable from the device (unlike passwords), you have high assurance of the user/device identities behind every network connection. Our Cloud RADIUS server was designed from the ground up to verify every certificate. It leverages powerful identity integrations to see and apply the latest policies in your identity infrastructure to determine in real-time which devices or authorized users should be allowed in the network and how much information they can access.
What Is Cloud Network Access Control (Cloud NAC)?
Cloud NAC is a network security model that enforces authentication and authorization using cloud-based identity providers and security signals instead of on-premise NAC appliances.
Cloud NAC verifies device identity, user identity, and security posture before granting network access. By integrating with identity providers, MDM platforms, and endpoint security tools, Cloud NAC enables Zero Trust network access without requiring endpoint agents.
How Does Cloud NAC Work?
Cloud NAC works by integrating authentication systems such as RADIUS with identity providers and device management platforms.
When a device attempts to connect to the network, the Cloud NAC system verifies user identity, device posture, and compliance status before allowing access. Policies can then segment users into different VLANs or network zones based on identity attributes.
What Is the Difference Between Cloud NAC and Traditional NAC?
Traditional NAC relies on on-premise appliances that inspect network traffic and enforce policies locally.
Cloud NAC replaces these appliances with cloud-based authentication and policy engines that integrate directly with identity providers and device management systems. This approach reduces infrastructure complexity while enabling Zero Trust network access.
What Cloud NAC Policies Can Be Configured in SecureW2?
With the Cloud NAC platform in our management portal, you can configure role-based, policy-based, and attribute-based access policies.
- Role-based access control (RBAC) assigns users permissions based on the organization's designated roles.
- Policy-based access control sets policies to manage user access to data and systems.
- Attribute-based access control applies access policies based on very granular attributes for precise decision-making, like name, email address, geographical location, or environmental attributes.
SecureW2 works with any attribute, role, or group from your identity or device management systems. This provides a foundational platform to enable highly automated network access control.
The most common policies configured in SecureW2 are for VLAN segmentation. Cloud RADIUS makes run-time-level policy decisions based on the attributes you configure in your certificates or the lookup during authentication to segregate authorized users into separate VLANs.
How Does Public Key Infrastructure (PKI) Enable More Robust Network Security Policies?
At a high level, you can identify with 100% accuracy the users/devices allowed on your network, enabling world-class segmentation. Public Key Infrastructure (PKI) allows your organization to implement the security of digital certificates. Certificate templates contain in-depth context that can be used to create policies, including factors such as:
- user attributes
- user groups
- device serial number
- user email
- operating system
- whether the device is managed or unmanaged
- issuing Certificate Authority (CA)
- model number
- MAC address
- certificate validity
Administrators can easily create policies around specific user groups, such as segmenting different departments into their VLANs. You can also create policies that put particular types of devices into their networks, such as preventing BYODs/unmanaged devices from accessing a given network.
Our unique managed PKI integrates seamlessly with your existing infrastructure to leverage the most up-to-date information. We have advanced integrations with MDMs like Intune Jamf that allow us to automatically revoke certificates when users are moved into particular smart or static groups. This ensures that only the most current access policies are consistently applied.
Why Should I Consider Transitioning Away from Password-Based Network Authentication?
Password-based authentication leaves your network resources vulnerable to security risks like Man-in-the Middle (MITM) and phishing attacks. Aside from direct attacks by hackers, your end-users may mismanage their passwords. Passwords also offer zero assurance around device trust, which is now required by the National Institute of Standards and Technology (NIST) for any organization doing research or working with federal entities.
There’s also the end-user experience to consider. Managing a plethora of ideally unique and complex passwords can be frustrating. Plus, users often forget, reuse, and even share passwords with friends, family, and colleagues. By using a passwordless form of authentication, such as digital certificates, your users no longer have to deal with the annoyance of creating new passwords or being disconnected from resources when their passwords expire.
Transitioning to a passwordless network authentication secures your network through phishing-resistant digital certificates. You can set specific policies to take complete control of your network.
How Do Your PKI and RADIUS Integrate with Our Infrastructure for Cloud NAC?
The SecureW2 PKI and Cloud RADIUS integrate with identity providers and MDM platforms to enable dynamic Cloud NAC enforcement.
At the time of enrollment, our PKI leverages information from your Identity Provider or device management platform, encoding those attributes in certificate templates. With Intune and Jamf, our PKI uses enhanced integrations, allowing for automatic certificate revocation. Cloud RADIUS integrates with all major cloud Identity Providers, but has enhanced integration with Azure AD (Entra ID), Google, Okta, and OneLogin.
Cloud RADIUS verifies a user’s status in any of the aforementioned IDPs in real-time. If you haven’t had time to revoke a certificate, the Cloud RADIUS Identity Lookup feature will deny network access if the user has been deactivated in your identity platform. This runtime enforcement ensures Cloud NAC policies remain continuously aligned with your identity infrastructure.
Can I Use the Security Policies from My Cloud Identity Provider on Your Cloud NAC Platform?
Yes. The SecureW2 Cloud NAC platform was designed with this specifically in mind.
Our Dynamic Policy Engine integrates with existing IDPs like Google, Okta, and Azure, which helps admins implement policy decisions during authentication. SecureW2 Cloud RADIUS allows you to enforce policies with user/device lookup in real-time against IDPs to ensure secure and efficient access management. This ensures Cloud NAC access policies automatically reflect device posture and compliance state.
Can I Leverage My Security Policies from my MDM with Your Platform?
You can seamlessly transfer security policies from your MDM to the SecureW2 Managed PKI. Our Managed PKI lets you transfer security policies from major MDMs like Jamf, Intune, and Mosyle, to name a few.
Integrating with our Managed Gateway API lets you use SCEP, JSON, and ACME to provide digital certificates to Windows, MacOS, iOS, and Google Chromebooks. You can now set policies and send configuration profiles to your managed devices for auto-enrollment and 802.1X authentication for effective policy enforcement.
With SecureW2, you can enable zero-touch issuance, renewal, and revocation of certificates. Our PKI employs advanced integrations with Intune and Jamf in particular. If you use Intune or Jamf, we can check specific groups in them every several minutes, automatically revoking certificates from devices in those groups.
Does Your Platform Offer Network Access Control Solutions for IoT Devices that Can’t Support Certificate-Based Authentication?
Cloud RADIUS supports MAC Authentication to provide network access control for devices that do not support 802.1X authentication, like printers and IoT devices. The SecureW2 Cloud RADIUS supports MAB and MAC address filtering. It segments your devices with a dynamic access list and VLAN assignments, so your less secure IoT devices are properly segmented from trusted, managed devices. You can easily upload .csv files, including all your devices, segment them into groups, and dynamically segment them into different VLANs.
How Can We Allow Guest Access Without Compromising Cloud NAC Security?
The SecureW2 Cloud NAC includes secure guest access through Web Authentication captive portals and JoinNow NetAuth.
Cloud RADIUS offers an easy-to-use Web Authentication captive portal as its first option. It works by presenting a captive portal when users join the network. After their credentials are validated, they are authorized to access the network. The MAC Address is saved for subsequent authentications and for admins to understand and track the users and devices using the network.
JoinNow NetAuth allows secure guest network access without compromising network security. Your guests can now access your network through self-registration or sponsored access. The JoinNow NetAuth also allows you to automate access policies where you can determine the level of access that can be provided to a guest on your network. Your guests can access an encrypted network combined with the SecureW2 JoinNow MultiOS.
What's the Difference Between Network Admission Control and Network Access Control?
Network Admission Control or Network Access Control prevents access to a network unless specific conditions and policies are met. Users and devices must authenticate when a corporate network is configured for NAC solutions before accessing corporate networks and applications.
NAC is enforced through various devices and solutions, like switches, routers, VPNs, and credential-based access. Network Admission Control denies access to unauthorized or non-compliant devices and quarantines them, thus securing network endpoints from unauthorized access, and security threats while enhancing network security.