In enterprise mobility environments, certificate issuance is no longer a static operation tied to simple directory lookups. As organizations move toward Zero Trust and conditional access enforcement in Microsoft ecosystems, confusion frequently arises around two enrollment models: traditional SCEP and the Intune CA Partner integration.
Although both ultimately result in a certificate being issued to a device, their authentication models, trust validation mechanisms, and failure modes are fundamentally different. Understanding the SCEP vs Intune CA partner distinction is critical, especially when troubleshooting common issues such as attribute mismatches, empty RFC fields, or failed device lookups in Microsoft Entra ID.
SCEP vs Intune CA Partner: Key Differences
Here are some of the most important features of traditional SCEP and Intune CA partner.
Traditional SCEP: Challenge-Based Enrollment
SCEP (Simple Certificate Enrollment Protocol) was designed in an era when enterprise networks were directory-centric and relatively static. The protocol allows a device to generate a key pair locally and submit a Certificate Signing Request (CSR) to a Certificate Authority (CA), typically through a Registration Authority (RA).
In most implementations, the validation mechanism hinges on a shared secret, commonly called a “challenge password.” That challenge is embedded inside the SCEP request. If the RA successfully verifies the challenge, certificate issuance proceeds.
This design makes a critical assumption: having the correct challenge grants authorization to receive a certificate.
In early on-premises environments, that was a reasonable trade-off. Devices were domain-joined. Networks were controlled. Certificate issuance volumes were predictable.
However, modern cloud-managed environments are not static. They are identity-driven. That is where SCEP deployments inside Microsoft Intune frequently encounter friction.
Attribute Lookup Failures: The Real Cause of Many “SCEP Intune” Issues
In Microsoft-based environments, certificate issuance rarely happens in isolation. Certificates are often used for:
- Wi-Fi authentication (EAP-TLS).
- VPN access.
- Intune SCEP authentication
- Conditional Access enforcement.
- Device identity binding.
To enable this, the certificate fields must align with the identity provider’s expectations.
One of the most common enrollment failures occurs during attribute lookup. Administrators may attempt to map certificate templates using attributes such as device serial numbers or custom identifiers. However, Microsoft Entra ID does not honor arbitrary identifiers for identity binding.
For lookups to succeed reliably, specific attributes such as the Azure Device ID and User Principal Name (UPN) must be correctly encoded in the certificate or mapped via supported mechanisms.
If the certificate is issued but identity binding fails downstream, administrators often interpret it as a “certificate problem.” In reality, it is an identity mapping problem.
The RFC Field Crisis
A recurring pain point in SCEP deployments is the “empty RFC field.” If the RFC field is not properly populated during the enrollment handshake, the device object may not be created correctly in Intune or Entra ID. When identity object creation fails, certificate issuance fails as a downstream consequence.
These are not flaws in the SCEP protocol itself; they are symptoms of trying to apply static validation models to a dynamic identity system that requires live signals.
Intune CA Partner: OAuth-Based Authorization Model
The Intune CA Partner integration fundamentally changes the trust model.
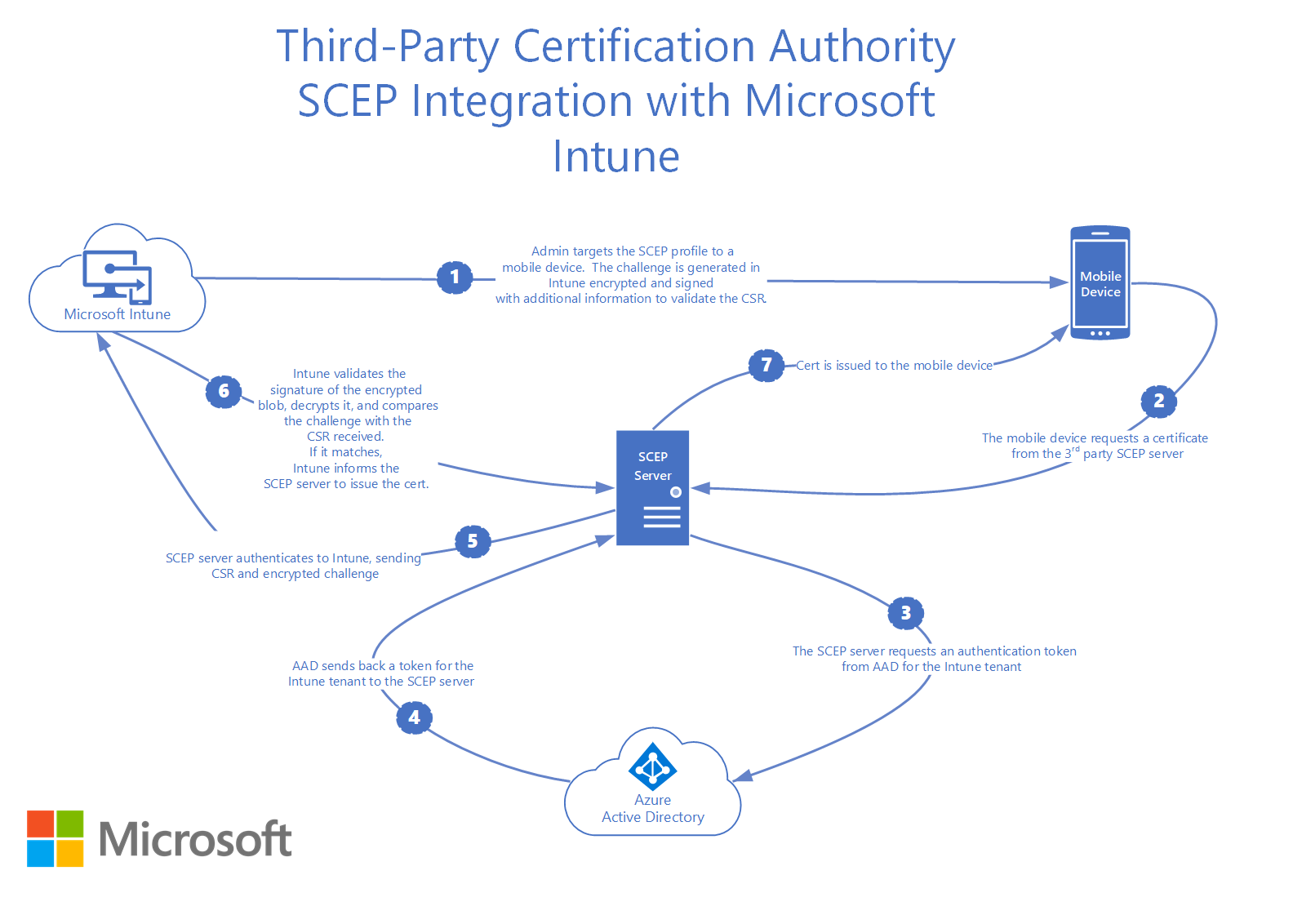
In this architecture, identity validation does not depend on a shared challenge embedded in the SCEP request. Instead, the process incorporates OAuth-based authentication backed by Microsoft Entra ID.
How the OAuth Model Operates
- The OAuth Intune certificate enrollment process replaces the static challenge with a secure, tokenized workflow:Device Initiation: The device initiates enrollment through an Intune profile.
- Token Generation: Intune communicates with Microsoft Entra ID to obtain a unique OAuth token.
- Authentication: The device uses this bearer token to authenticate the request to the CA.
- Live Validation: The CA partner validates the token directly with Microsoft to ensure the device is active, compliant, and authorized.
The critical shift here is that authentication is decoupled from the SCEP payload. The identity validation does not rely on a challenge string but on OAuth-based identity proofing tied to Entra ID.
This is significantly more aligned with modern cloud-native security models.
Architectural Difference: Static vs Dynamic Identity Binding
There has been a fundamental shift from the legacy, manual dependencies of SCEP/NDES to the automated, API-driven workflows of modern cloud-native CA integrations, as follows:
| Feature | Traditional SCEP (NDES) | Intune CA Partner (SecureW2) |
| Auth Mechanism | Shared Challenge Password | OAuth 2.0 Bearer Tokens |
| Identity Lookup | Static / LDAP-based | Dynamic / Live API signals |
| Infrastructure | Requires NDES & Connectors | Cloud-Native / No On-prem Footprint |
| Validation | Point-in-time (Issuance only) | Continuous (Live Status Check) |
| Failure Logging | Obscure / Silent failures | Clear API-driven diagnostic logs |
At a surface level, both traditional SCEP and the Intune CA Partner model result in a certificate being installed on a device. However, the real difference lies not in the protocol wrapper but in how identity is validated and how trust is anchored during enrollment.
Traditional SCEP assumes that authorization can be inferred from possession of a shared secret. Modern Microsoft ecosystems assume identity must be validated through dynamic, token-based mechanisms.
This difference becomes critical when implementing Zero Trust certificate-based authentication. Conditional Access requires identity confidence. A shared challenge string does not meet that bar.
When to Use Traditional SCEP vs. Intune CA Partner
SCEP is not obsolete. It remains functional in environments where identity systems are static and cloud integration is minimal.
However, most enterprises using Microsoft Intune today operate in hybrid or cloud-first environments. In those scenarios, the limitations of static challenge-based validation become more pronounced.
The question is not whether SCEP works, but whether it can keep pace with the automated, continuous verification required by modern Zero Trust architectures.
When Traditional SCEP Can Still Make Sense
Traditional SCEP is best suited for environments with physically or logically isolated networks, legacy devices, systems without Entra ID integration, and a stable, controlled, and static device population.
In these environments, dynamic OAuth orchestration may not be necessary.
However, once identity enforcement moves into Entra ID and Conditional Access policies, static challenge-based enrollment creates blind spots.
Why Dynamic SCEP Wins in 2026
Traditional SCEP assumes authorization can be inferred from a secret. Modern Microsoft ecosystems assume identity must be validated through dynamic, token-based mechanisms. This difference is vital for Conditional Access. A shared challenge string cannot tell you if a device was unenrolled five minutes ago; an OAuth token validated against a live directory can.
When OAuth-Backed CA Partner Integration Becomes Essential
Cloud-managed environments typically use certificate-based authentication for Wi-Fi or VPN, often involving Microsoft Intune, Microsoft Entra ID, and Conditional Access, where a robust Intune CA partner setup is no longer optionalOAuth-backed CA integration is no longer optional.
It ensures that:
- Certificate issuance is tied to valid Azure AD device objects.
- Identity validation occurs before certificate delivery.
- Attribute mapping aligns with Microsoft-supported identifiers.
- Enrollment failures are visible and diagnosable rather than silent misbindings.
More importantly, it eliminates hidden fragility caused by improper RFC field configuration or misaligned identity attributes, two of the most common failure points in SCEP Intune deployments.
SecureW2: Modernizing Intune Certificate Enrollment
Modern Intune deployments require more than just successful certificate issuance; they require identity-aligned issuance. Static challenge-based SCEP workflows often introduce fragility through misconfigured attributes, unsupported identifiers, or improper RFC mapping, leading to downstream authentication failures that are difficult to diagnose.
Our dynamic PKI and Intune CA Partner integration is built specifically for Microsoft’s OAuth-based identity model. Instead of relying on shared challenges and rigid templates, SecureW2 validates identity through Entra ID during enrollment, ensuring certificates are properly bound to Azure AD device objects from the start. Subject and SAN attributes are aligned with supported identifiers, such as Azure Device ID and UPN, reducing lookup failures and preventing broken identity mappings.
Beyond enrollment, we streamline certificate lifecycle management with centralized visibility into issuance, search, and revocation, making it easier to support Conditional Access, certificate-based Wi-Fi, and Zero Trust architectures at scale.
If your SCEP Intune deployment is experiencing identity binding issues or inconsistent authentication behavior, we provide a structured, OAuth-backed approach that ensures certificate enrollment is secure, scalable, and cloud-aligned. Schedule a free, personalized demo to learn what SecureW2 solutions can do for your organization.