Key Points
- Network hubs operate at Layer 1 of the OSI model, connecting multiple devices and broadcasting to every port with no traffic management.
- Hubs’ simple design and lack of encryption leaves them open to security vulnerabilities and can cause bandwidth issues.
- Better networking solutions today like routers and CloudRADIUS allow for multi-layer network security.
The rapid pace of technological development over the past several decades has seen many tools and types of software rise to prominence only to be replaced by more sophisticated technologies. Such is the case for network hubs, which allow different devices linked together in a network to talk to each other. While no longer an ideal solution, network hubs laid the groundwork for networking devices like switches and routers widely used across workplaces today.
What is a Network Hub?
A network hub is a tool that physically connects multiple devices in a Local Area Network (LAN) via cables. Network hubs can include anywhere from 4 to 24 ports allowing them to connect devices on a network.
Network hubs operate on Layer 1 of the Open Systems Interconnection (OSI) model, meaning they handle physical data transmission and cannot specify which device should receive the data.
Hubs essentially act as repeaters to pass raw bits of data from one device to another, following standard Ethernet specifications for signal transmission. However, because hubs lack the intelligence to determine where to send that data, the data is broadcast to all connected devices. Network hubs are much simpler than modern networking setups, which rely on secure wired solutions to allow encryption and access control while achieving similar connectivity.
In decades past, network hubs were a cost-effective way to connect multiple computers and share data. However as technology and security practices have evolved they no longer provide an ideal, or safe, way of linking devices together in a network.
A brief overview of network hubs’ uses and drawbacks:
- Basic broadcasting: Acts as a central connection point, broadcasting data to all connected devices.
- Single collision domain: Traffic collisions can occur if more than one device is trying to send data at a time.
- No data traffic management: Hubs can’t determine where to send traffic.
- Simplicity and cost: Despite their limitations, hubs offered a simple, cost-effective solution for setting up local networks.
While network hubs’ are mostly obsolete today, they are still useful in some cases, like very basic networks without security concerns.
How Do Network Hubs Work?
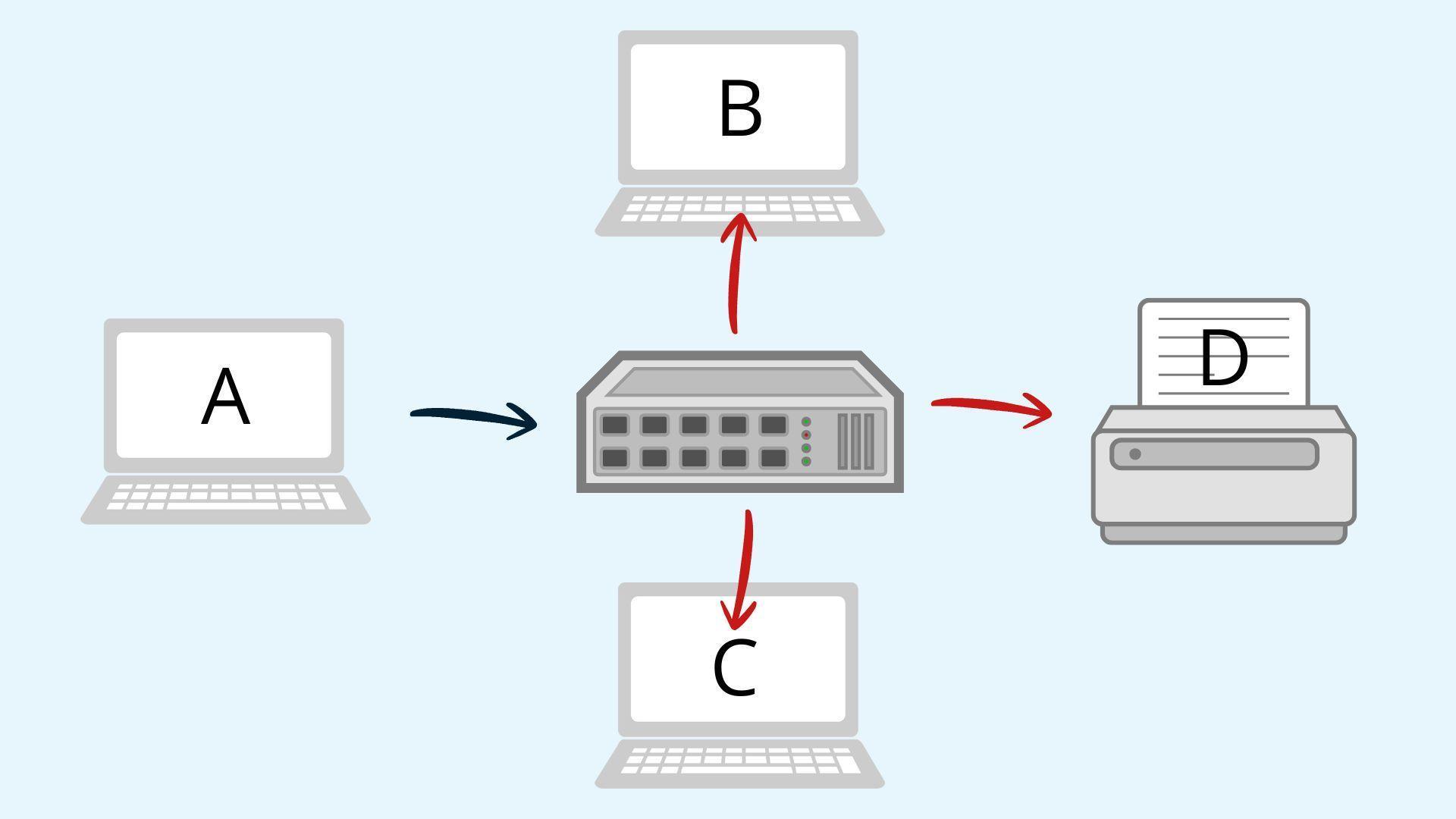
A network hub sits between devices linked together in a network, routing data to the correct locations.Network hubs receive a data packet from one device (like a print job or web request) and send it to all other devices on the network. Because hubs operate at Layer 1 of the OSI model, they only transmit the data and don’t read or interpret it.
Here’s an example of how network hubs work:
Imagine a small network with your computer, a printer, and two other devices all connected to a single hub. Let’s say you want to print a document. When you click print, your computer sends a data packet to the hub.
This packet includes information like:
- Destination Media Access Control (MAC) address: Which device should process the information (the printer).
- Source MAC address: Where the data is coming from and where to address any responses (your computer).
- Payload: The actual content or request being sent (what to print).
- Cyclic Redundancy Check (CRC)/checksum: Error checking to ensure the data arrives correctly.
The hub then broadcasts this data to all connected devices. Because the packet contains the source address only the printer acts on the request.
Broadcasting the data to all connected devices regardless of need has two obvious downsides:
- Bandwidth limitations: The network is carrying more data than is needed, which can slow transmission speeds and lead to data collisions.
- Security vulnerabilities: This model assumes that every device, other than the intended recipient, will ignore data. This leaves room for bad actors to receive data that was not intended for them. Packet sniffers can detect and view any unencrypted information.
Common Types of Network Hubs
Network hubs can be broken down into a few types, each with its own advantages and disadvantages.
Passive Hubs
Passive network hubs are the most basic form of network hub. They connect devices without external power, acting as a physical connector for small, short-distance networks. While they are cost-effective and simple to use for small networks, passive hubs’ signals weaken with distance increase the odds of data collisions.
Active Hubs
Active hubs need external power to operate, and regenerate and amplify signals before broadcasting them to all connected devices. Active hubs typically have stronger, cleaner signals than passive hubs and can transmit data farther, but are still limited when it comes to security. These hubs still experience data collisions, lack traffic intelligence, and are less efficient than network switches.
Intelligent Hubs
Intelligent hubs add networking monitoring capabilities. They can detect issues like faulty or disconnected ports, signal quality problems, and abnormal traffic patterns. While intelligent hubs can detect these problems, they still can’t prevent collisions, segment traffic, or enforce security protocols.
Here’s how these various hubs stack up against each other:
| Feature | Passive Hub | Active Hub | Intelligent Hub |
| Power required | No | Yes | Yes |
| Signal amplification | No | Yes | Yes |
| Traffic control | No | No | Limited |
| Network monitoring | No | No | Yes |
| Data collisions | High | High | High |
| Cost | Low | Medium | High |
| Modern usage | Rare | Very rare | Mostly obsolete |
Network Hub Security Vulnerabilities
Network hubs’ security vulnerabilities are the primary reason they are no longer in general use.
Hubs invite the following security concerns:
- Lack of encryption: They can’t add encryption when sending information across the network
- No segmentation: Hubs can’t divide the network into individual subnetworks for specific devices or users
- Network congestion: Because hubs broadcast all transmitted data to every connected device and create a single collision domain, they use up bandwidth and slow network traffic.
- Vulnerability to eavesdropping: Attackers using packet sniffers can easily capture any unencrypted traffic that is broadcast over the network
Modern security approaches reduce or eliminate these concerns altogether by allowing data segmentation, encryption, and the use of authentication to prevent unauthorized parties from accessing data they shouldn’t.
Network Hub Security Protocols vs. Modern Security Solutions
Due to their architecture and operation at the physical level of the OSI model, network hubs don’t utilize any native security protocols. Without the capability to read or interpret data, a network hub can’t enforce protocols that rely on addressing, authentication, or encryption.
Security protocols require a device operating at OSI Layer 2 or higher. Companies today use modern solutions like network switches and routers that allow for enhanced security features.
These include:
- VLANs (Virtual Local Area Networks): Segment devices into different, isolated network groups so traffic is limited to its own virtual network.
- Port security: Specifies the MAC addresses and number of connections that are allowed to connect to a specific port.
- Access control lists (ACLs): Rules created to specify which users can access certain files, folders, or networks and any restrictions to their access.
- Encryption and authentication protocols: Ensure user verification and securely encode data that is transmitted over the network.
Alongside modern devices platforms like RADIUS (Remote Authentication Dial-In User Service) and protocols like EAP-TLS (Extensible Authentication Protocol-Transfer Layer Security) work with switches, routers, and Wi-Fi access points to authorize devices before they can join. While the switch or router enforces traffic rules, RADIUS acts as an authority, checking credentials and certificates so only approved devices gain access.
Network Hub vs. Network Switch
Today, network hubs have been largely replaced by network switches.While these devices appear similar on the surface, they function differently.
Network switches physically connect devices just as hubs do, but they have more advanced capabilities:
- Data handling: Switches primarily operate on Layer 2 of the OSI model and are able to read relevant information from data packets. The ability to use MAC addresses to route traffic allows the switch to transmit data to specific devices rather than to every device on the network.
- Performance: Because switches establish direct communication between devices, they improve network efficiency and reduce collisions.
- Security: Data exposure is limited when data is only transferred to its intended recipient and not broadcast to all connected devices. Switches can also work with network access control services to ensure only authorized users can join the network.
- Scalability: Switches can support much larger networks than hubs are able to. Switches generally have 8, 24, or 48 ports (or sometimes more) and can be chained together to further expand the network.
Modern networks using switches can also leverage solutions like CloudRADIUS to simplify device authentication and enforce secure access for authorized users.
Are Network Hubs Ever Used Today?
Due to security vulnerabilities, performance limitations, and advancements in network technology, network hubs are far from the recommended solution for modern networks. That being said, they are sometimes used in certain environments.
Some legacy equipment must still use hubs because they are unable to connect to modern switches. Replacing older equipment can be costly, so using using a hub can be a worthwhile tradeoff.
In other instances like in a classroom or home office with a very small network and no security risks, a hub may be more suitable for connecting a few devices.
As technology progresses and networking needs and security practices grow more complex, it’s imperative to safeguard data and assets with the best security protocols. Network hubs, while once a useful tool, no longer meet the needs of most organizations today. Learn more about how to update to best-in-class security protocols and technology in the SecureW2 blog, and schedule a free demo at any time to learn more.