Key Points
- Public key encryption uses asymmetric keys and digital certificates to protect data and verify identities online.
- It underpins secure protocols like SSL/TLS and strengthens authentication over wireless and web networks.
- Implement a managed PKI to safeguard private keys, automate certificate management, and secure your organization.
Public key encryption is the cryptographic foundation behind secure web browsing, digital signatures, and certificate-based network authentication. It uses a mathematically linked key pair — one public, one private — to encrypt and decrypt data without ever sharing a secret key over the wire.
This guide covers how public key encryption works, how it compares to symmetric encryption, where it fits into protocols like Transport Layer Security (TLS) and Extensible Authentication Protocol-Transport Layer Security (EAP-TLS), and how organizations use it through Public Key Infrastructure (PKI) to authenticate users and devices on their networks.
What Is Public Key Encryption?
Public key encryption (also called asymmetric encryption or public key cryptography) is a method of encrypting data using two separate but mathematically related keys: a public key and a private key.
The public key can be shared openly. Anyone who has it can encrypt a message. But only the corresponding private key can decrypt that message. The reverse also works: data signed with a private key can be verified by anyone holding the matching public key.
This asymmetry solves a problem that plagued symmetric encryption for decades: how do two parties agree on a shared secret without an attacker intercepting it? With public key encryption, the public key travels freely. The private key never leaves the owner’s control. Public key cryptography is widely used today for securing web traffic and for network security protocols. It puts the “S” in “HTTPS”.
The Math Behind Pubic Key Encryption
Public key cryptosystems rely on mathematical problems that are easy to compute in one direction but computationally infeasible to reverse. The most common examples:
- Integer factorization: Rivest-Shamir-Adleman (RSA) encryption relies on the difficulty of factoring the product of two large prime numbers.
- Discrete logarithm: Diffie-Hellman key exchange and Digital Signature Algorithm (DSA) depend on the difficulty of computing discrete logarithms in a finite field.
- Elliptic curve: Elliptic Curve Cryptography (ECC) uses the discrete logarithm problem applied to points on an elliptic curve, achieving equivalent security with shorter key lengths.
These mathematical foundations mean that even with access to the public key, deriving the private key requires computational effort that exceeds what modern (and near-future) hardware can deliver in any reasonable timeframe.
Public Key Encryption vs. Private Key Encryption
Understanding the difference between symmetric and asymmetric encryption is fundamental to understanding where each method fits in modern security. Here is a table breaking down the features of public key encryption and private key encryption:
| Feature | Public Key (Asymmetric) Encryption | Private Key (Symmetric) Encryption |
| Keys | Two keys — one public, one private | One shared secret key |
| Key distribution | Public key shared openly; no secure channel needed | Requires a secure channel to share the key |
| Speed | Slower — complex mathematical operations | Faster — simpler algorithms (e.g., AES, ChaCha20) |
| Use cases | Key exchange, digital signatures, certificate authentication | Bulk data encryption, session encryption |
| Key length | RSA 2048-bit or 4096-bit; ECC 256-bit | AES 128-bit or 256-bit |
| Risk | Private key compromise exposes decryption capability | Key compromise exposes all encrypted data |
In practice, most modern protocols use both. TLS, for example, uses asymmetric encryption during the handshake to establish a shared session key, then switches to symmetric encryption for the actual data transfer. This hybrid approach combines the security of asymmetric key exchange with the speed of symmetric encryption.
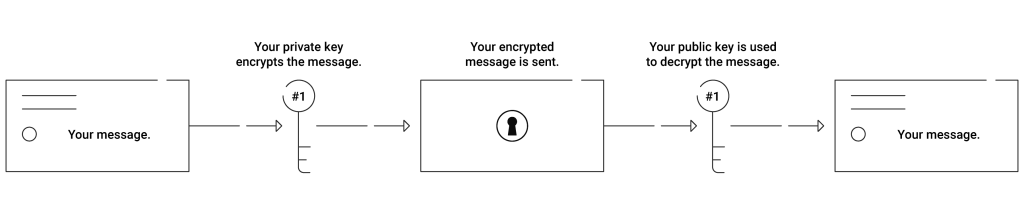
How Public Key Encryption Works (Step by Step)
Here is how asymmetric encryption works in a typical communication scenario:
- Key pair generation: The recipient generates a public-private key pair using an algorithm like RSA or ECC. The public key is published or shared. The private key is stored securely.
- Encryption: The sender obtains the recipient’s public key and uses it to encrypt the message. The resulting ciphertext is unreadable without the private key.
- Transmission: The encrypted ciphertext travels over the network. Even if intercepted, it cannot be decrypted without the private key.
- Decryption: The recipient uses their private key to decrypt the ciphertext back into readable plaintext.
The formula is straightforward:
- Encrypt: Plaintext + Public Key = Ciphertext
- Decrypt: Ciphertext + Private Key = Plaintext
This process works because the mathematical relationship between the two keys allows one to reverse the operation of the other, but only in the correct direction.
Digital Signatures and Public Key Encryption
Public key encryption does more than protect confidentiality. It also provides authentication and integrity through digital signatures.
A digital signature works in reverse compared to encryption:
- The sender applies a hash function (such as SHA-256) to the message, producing a fixed-length digest.
- The sender encrypts the hash with their private key. This encrypted hash is the digital signature.
- The sender transmits the message along with the signature.
- The recipient decrypts the signature using the sender’s public key, recovering the hash.
- The recipient independently hashes the received message and compares the two hashes. If they match, the message is authentic and unaltered.
Digital signatures prove three things: the identity of the sender (authentication), the message was not modified in transit (integrity), and the sender cannot deny having sent it (non-repudiation).
This mechanism is the backbone of digital certificates, code signing, and document verification across the internet.
Public Key Encryption Algorithms
Several algorithms implement public key encryption, each with different strengths.
The RSA Algorithm
RSA remains the most widely deployed asymmetric algorithm. Published in 1977, it derives its security from the difficulty of factoring the product of two large prime numbers. RSA supports both encryption and digital signatures.
Modern implementations use 2048-bit or 4096-bit key lengths. RSA is the default for most TLS certificates and is supported across virtually all platforms and libraries.
The ECC Algorithm
ECC applies the discrete logarithm problem to points on an elliptic curve. It achieves the same security as RSA with significantly shorter keys — a 256-bit ECC key provides roughly equivalent security to a 3072-bit RSA key.
Shorter keys mean faster computations and lower bandwidth overhead, making ECC the preferred choice for mobile devices, IoT, and performance-sensitive applications. ECC is used in ECDSA (digital signatures) and ECDH (key exchange).
The DSA Algorithm
DSA was proposed by the National Institute of Standards and Technology (NIST) in 1991 as a federal standard for digital signatures. While RSA handles both encryption and signing, DSA is limited to signature generation and verification. DSA adoption has declined in favor of ECDSA, which offers better performance at equivalent security levels.
Diffie-Hellman Key Exchange
Diffie-Hellman is not an encryption algorithm itself but a key exchange protocol that uses public key cryptography principles. It allows two parties to establish a shared secret over an insecure channel without transmitting the secret directly. Modern TLS implementations commonly use Ephemeral Diffie-Hellman (DHE) or its elliptic curve variant (ECDHE) to provide forward secrecy.
Public Key Encryption and Digital Certificates
A digital certificate binds a public key to a verified identity — a person, device, server, or organization. Certificates are the mechanism that makes public key encryption practical at scale.
How Certificates Work
A Certificate Authority (CA) verifies the identity of the certificate requestor, then signs a digital certificate containing:
- The subject’s identity (domain name, organization, or device identifier)
- The subject’s public key
- The CA’s digital signature
- Validity period
- Serial number and revocation information
When a client connects to a server, the server presents its certificate. The client verifies the CA’s signature against its trusted root store. If the signature checks out, the client trusts the public key in the certificate and uses it to establish an encrypted session.
X.509 Standard
Most digital certificates follow the X.509 standard, which defines the format for public key certificates, certificate revocation lists (CRLs), and certificate path validation. X.509 certificates are used in TLS/SSL, email encryption (S/MIME), VPN authentication, and Wi-Fi network access (802.1X).
Public Key Infrastructure
PKI is the system of hardware, software, policies, and procedures that manages the lifecycle of digital certificates — issuance, distribution, renewal, and revocation. A PKI includes:
- Root CA: The top-level certificate authority whose certificate is self-signed and pre-loaded in trust stores
- Intermediate CAs: Subordinate CAs that issue end-entity certificates, creating a chain of trust back to the root
- Registration Authority (RA): Handles identity verification before certificates are issued
- Certificate Revocation Lists (CRLs) and OCSP: Mechanisms for revoking compromised or expired certificates
Organizations that need to issue certificates for internal users, devices, and servers operate their own PKI — either on premises with solutions like Microsoft AD CS, or through a managed cloud service.
How TLS Uses Public Key Encryption
TLS is the most visible application of public key encryption. Every HTTPS connection uses it.
During the TLS handshake:
- The client sends a “Client Hello” with supported cipher suites.
- The server responds with its TLS certificate (containing its public key) and chosen cipher suite.
- The client verifies the certificate against its trusted CA store.
- Using the server’s public key, the client and server negotiate a shared session key through a key exchange protocol (typically ECDHE).
- Both parties switch to symmetric encryption using the session key for the remainder of the connection.
This hybrid approach — asymmetric for the handshake, symmetric for data transfer — balances security with performance.
EAP-TLS: Public Key Encryption for Network Authentication
EAP-TLS extends the TLS mechanism to network authentication, and it represents the most secure method for controlling access to Wi-Fi and VPN networks. Unlike password-based protocols such as PEAP-MSCHAPv2, EAP-TLS uses mutual certificate-based authentication:
- The RADIUS server presents its certificate to the client.
- The client presents its own certificate to the server.
- Both sides verify certificates before authentication completes.
This mutual authentication eliminates credential theft, phishing, and man-in-the-middle attacks because there are no passwords to steal or intercept. Each device holds a unique digital certificate with a private key that never leaves the device.
SecureW2 JoinNow Cloud RADIUS and JoinNow Dynamic PKI automate certificate issuance and EAP-TLS authentication for enterprise Wi-Fi and VPN. Cloud RADIUS performs real-time identity lookups against identity providers like Entra ID, Okta, and Google Workspace — verifying not just the certificate, but the user’s current status and device compliance at every connection.
Is Public Key Encryption Secure?
Public key encryption, when implemented correctly with modern algorithms and adequate key lengths, is highly secure. A 2048-bit RSA key or 256-bit ECC key offers security margins that resist brute-force attacks with current and foreseeable computing power.
However, the system is only as secure as its weakest link:
- Private key compromise: If a private key is stolen, all encrypted communications and digital signatures tied to that key are compromised. Proper key storage (HSMs, TPMs) mitigates this risk.
- CA compromise: If a CA’s private key is breached, every certificate it issued becomes untrustworthy. Certificate transparency logs and CAA records help detect unauthorized issuance.
- Algorithm weaknesses: Quantum computing poses a long-term threat to RSA and ECC. Post-quantum cryptography (PQC) algorithms, standardized by NIST in 2024, are designed to resist quantum attacks. Organizations running cloud-hosted PKI can migrate to PQC algorithms without replacing on-premises hardware — a significant advantage over legacy PKI deployments.
- Implementation flaws: Weak random number generators, side-channel attacks, and improper key management cause more real-world breaches than mathematical breaks of the algorithms themselves.
Safely Storing Private Keys
The security of any public key cryptosystem depends entirely on protecting the private key. If an attacker obtains a private key, they can decrypt all data encrypted with the corresponding public key and forge digital signatures.
Hardware Security Modules
Hardware Security Modules (HSMs) are dedicated cryptographic processors that generate, store, and manage private keys in tamper-resistant hardware. HSMs provide:
- True random number generation for key creation
- Physical tamper detection and response
- Cryptographic operations performed inside the module (keys never leave)
- Audit logging for all key operations
HSMs are the standard for protecting CA private keys, TLS server keys, and any high-value cryptographic material.
Device-Level Key Protection
For endpoint devices, the best practice is to generate the private key on the device itself and prevent it from being exported. Then, even if the certificate is copied, it cannot be used on another device.
SecureW2 Dynamic PKI uses ACME Device Attestation and Dynamic SCEP issuance protocols to generate hardware-bound certificates where the private key is tied to the device’s TPM or Secure Enclave. Combined with CertIQ ML Anomaly Detection, organizations get real-time visibility into certificate activity and automatic detection of spoofed or duplicated certificates.
Strengthen Your Network with Certificate-Based Authentication
Public key encryption is the technology that makes certificate-based authentication possible. Every digital certificate, every TLS handshake, and every EAP-TLS network authentication relies on the asymmetric key pair at its core.
For organizations looking to move beyond passwords and secure network access with digital certificates, we provides a complete, cloud-native PKI and RADIUS platform. JoinNow Dynamic PKI automates certificate issuance with hardware-bound private keys, and JoinNow Cloud RADIUS enforces identity-driven access policies at every Wi-Fi and VPN connection.
Schedule a demo to see how SecureW2 replaces passwords with certificates.
Frequently Asked Questions
What is the difference between public key encryption and symmetric encryption?
Public key encryption (asymmetric encryption) uses two mathematically related keys — a public key for encryption and a private key for decryption. Symmetric encryption uses a single shared key for both operations. Asymmetric encryption is more secure for key exchange but slower, so most protocols use a hybrid approach: asymmetric encryption to exchange a symmetric session key, then symmetric encryption for bulk data transfer.
How is public key encryption used in TLS/SSL?
During a TLS handshake, the server sends its digital certificate containing its public key. The client verifies the certificate, then both sides use asymmetric key exchange (typically ECDHE) to negotiate a shared session key. The session key is then used for symmetric encryption of all subsequent data. This combination provides both the security of asymmetric key exchange and the performance of symmetric encryption.
Can public key encryption be broken by quantum computers?
Current quantum computers cannot break public key encryption in practice. However, sufficiently powerful quantum computers could theoretically break RSA and ECC using Shor's algorithm. NIST finalized post-quantum cryptography standards in 2024, including ML-KEM and ML-DSA, to address this future risk. Organizations using cloud-managed PKI are better positioned to migrate to post-quantum algorithms because the upgrade happens at the service level, not on individual hardware appliances.
What is the role of a Certificate Authority (CA) in public key encryption?
A Certificate Authority is a trusted organization that issues digital certificates binding a public key to a verified identity. The CA verifies the requestor's identity, then signs the certificate with its own private key. When others receive the certificate, they can verify the CA's signature to confirm the public key belongs to the claimed identity. CAs form the root of trust in PKI, enabling encrypted and authenticated communication at internet scale.
Why do enterprises use certificate-based authentication instead of passwords?
Passwords are vulnerable to phishing, credential stuffing, brute-force attacks, and man-in-the-middle interception. Certificate-based authentication replaces passwords with digital certificates containing public-private key pairs unique to each user and device. The private key never traverses the network, eliminating credential theft as an attack vector. Protocols like EAP-TLS use mutual certificate authentication for Wi-Fi and VPN access, providing phishing-resistant, passwordless network security.