Key Points
- PKI-as-a-Service (PKIaaS) is a cloud-based service that simplifies and modernizes public key infrastructure (PKI) management, eliminating the need for on-premise infrastructure.
- PKIaaS improves security and efficiency by automating critical processes like key management and certificate lifecycle management.
- PKIaaS offers enhanced scalability, rapid deployment, and simplified management by offloading complex tasks to a service provider.
PKI-as-a-service offers a managed PKI delivered through the cloud to automate key processes like certificate lifecycle management. Public Key Infrastructure (PKI) is the framework of policies, hardware, and software used to manage secure data transmissions with digital certificates. PKI lets you create, manage, distribute, use, store, and revoke certificates, using end-to-end encryption and identity authentication to keep data secure.
Managing PKI in-house can be daunting, requiring expert staff, ongoing maintenance, and on-premises hardware. But PKI-as-a-Service (PKIaaS) simplifies everything.
PKIaaS is a managed, cloud-based solution providing PKI functionalities that eliminate the need for on-prem infrastructure. PKIaaS makes robust security accessible to all organizations, even those without extensive IT departments.
In this article, we’ll define what PKIaaS is, how it works, its core components, and the benefits it offers. We’ll also explore the process of migrating from on-prem to managed PKI.
What Is PKI-as-a-Service (PKIaaS)?
PKI-as-a-Service (PKIaaS) is a cloud service providing full Public Key Infrastructure (PKI) functionality without on-prem infrastructure. This managed service simplifies your PKI by automating key generation and certificate management within a secure cloud-based platform.
With PKIaaS, organizations get the security and compliance of a full PKI framework, combined with the cost-efficiency and simplicity of the cloud. That means continuous trust architecture, cryptographic security, and identity verification, all with the cost-efficience and simplicity of a managed service.
How PKIaaS Works: Core Components
What’s included with PKIaaS? Here are the primary components:
Cloud Hosting
PKIaaS leverages cloud infrastructure to host the PKI, eliminating the need for physical hardware and ensuring high availability, redundancy, and disaster recovery. Cloud infrastructure also optimizes resources and facilitates rapid scaling.
Key and Certificate Automation
Automation in PKIaaS covers digital trust processes including key generation, digital certificate issuance, renewal, and revocation. Automating these processes drastically reduces the risk of human error and enforces real-time policy updates, while maintaining the integrity and security of digital signatures and encrypted communications.
Security Protocols and Public Key Cryptography
Robust security protocols are foundational to PKIaaS. By leveraging public key (asymmetric) cryptography, the service uses paired keys to ensure secure data encryption and seamless key exchange.
Public Key
The public key is openly distributed. It transforms plain text into an encrypted format; no one can decipher it without the matching private key. That’s why the public accessibility of this key isn’t a risk.
Private Key
The private key is closely guarded and never shared. It’s the only way to decrypt data encrypted by the public key. The security of the entire system hinges on keeping the private key confidential.
Importance of the Public and Private Keys for Data Integrity and Confidentiality
Public and private keys work together to maintain integrity and confidentiality. When encrypted using a public key, only the corresponding private key can decrypt data. This keeps data and digital signatures secure and intact during transmission.
Managed Services
PKIaaS offers managed services, including setup, ongoing maintenance, and support. These services ensure private keys, digital certificates, and cryptographic algorithms are properly configured and maintained, providing end-to-end encryption and secure communications.
How Certificate Lifecycle Management (CLM) works in PKIaaS
PKIaaS manages the entire certificate lifecycle, from issuance to revocation. This includes systems and processes such as:
- Certificate Authorities: PKI certificate management includes selecting trusted certificate authorities (CAs), which are organizations that serve as the official governing administrator of digital certificates.
- Certificate Issuance: PKIaaS manages issuance, enlisting CAs to sign and deliver the certificates that manage access to networks and resources.
- Certificate Renewal: PKIaaS also handles automated certificate renewal, preventing accidental expired certificates and maintaining secure connections.
- Certificate Revocation: PKIaaS checks the issuing CA’s certificate revocation list (CRL) to deny access or invalidate previously active certificates. Automated revocation instantly invalidates compromised or expired certificates, ensuring continuous security compliance.
Authentication and Authorization in PKIaaS
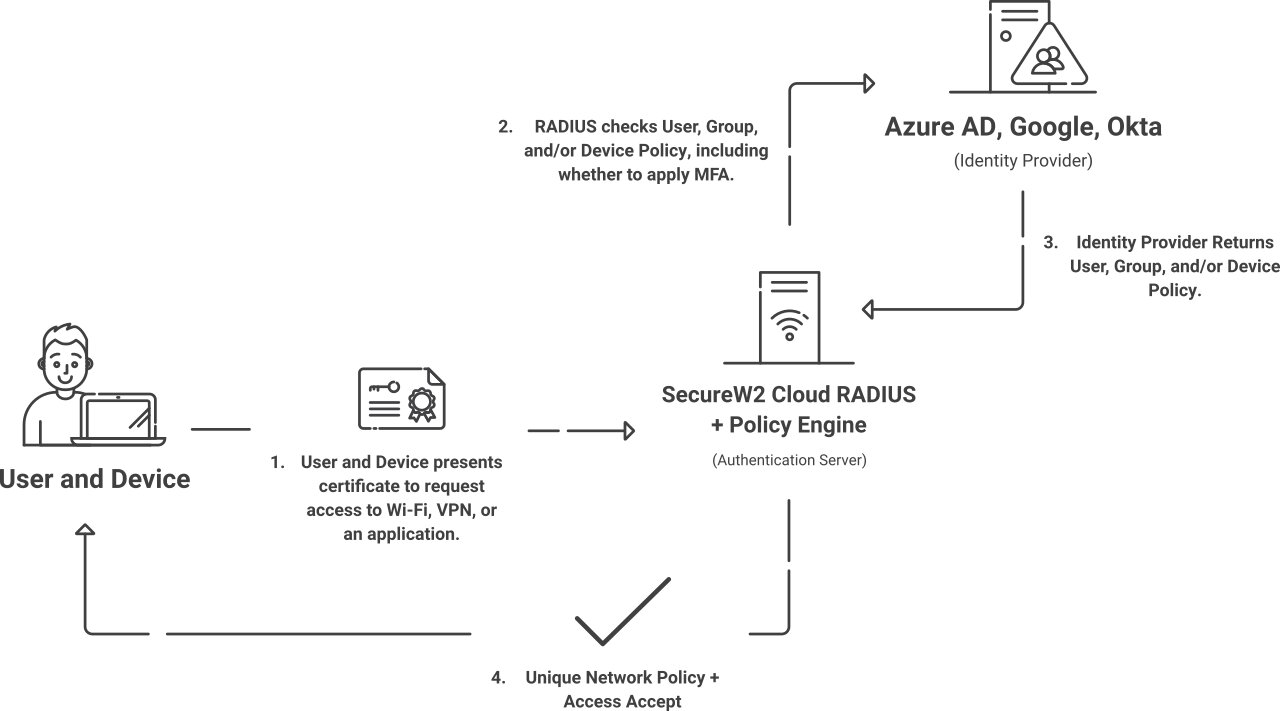
PKIaaS provides robust authentication and authorization mechanisms. It uses certificates to verify user and device identities, granting appropriate access based on predefined security policies. PKIaaS providers use modern protocols for seamless, reliable verification and access controls.
PKIaaS vs. AAA (Authentication, Authorization, Accounting)
PKI is not an Authentication, Authorization, Accounting (AAA) protocol.
The AAA framework is a network access control (NAC) protocol for transmitting sensitive data, particularly over wireless networks. AAA servers help routers securely authenticate (verify user credentials), authorize (allow access), and account (record user/access details) all attempts to access the network.
Traditional and cloud-based PKIs provide authentication for certificate requests by verifying the identity of users and devices. They also authorize access once authenticated.
But traditional PKIs don’t provide built-in accounting — a critical security measure.
Many managed PKI service providers, including the SecureW2 JoinNow Platform, include accounting for improved security, compliance, and audit management.
PKI vs. Other Services
PKI is sometimes confused with other similar or related services. We’ll clear up the confusion with a few explanations.
PKIaaS vs. SSL
PKI and SSL both relate to certificate lifecycle management (CLM), but in different ways.
Public Key Infrastructure (PKI) provides the infrastructure to enable CLM, such as certificate authorities (CA) and registration authorities (RA). It contains everything an organization needs to issue, store, renew, revoke, and otherwise manage digital certificates.
Secure Sockets Layer (SSL) is one component of CLM This protocol creates an encrypted link between a web server and a browser, ensuring that all data, including digital certificates, remains private and secure. Today, most organizations use a modernized form of encryption called Transport Layer Security (TLS), though “SSL” is still the common industry term for both protocols.
So, while PKI supports the performance of certificate lifecycle automation and management, SSL is a specific way to verify certificates within the larger CLM process.
PKI vs. IAM
PKI and IAM both manage access, but at different structural levels.
PKI is a specific type of infrastructure implemented to secure data and communications through digital certificate encryption with both private and public keys (hence, Public Key Infrastructure). PKI employs various authentication methods and authorization methods to reduce unauthorized access.
IAM, or Identity and Access Management, is a broader framework for organizational security. It involves specific policies and tools dictating which networks, resources, and data a specific user or device can access.
Secure PKI may be one tool used in a larger IAM strategy.
PKI vs. API
PKI stands for Public Key Infrastructure, a system relying on both public and private keys (asymmetric cryptography) to encrypt data using digital certificates.
API stands for Application Programming Interface, a method of connecting distinct software systems for seamless operation without revealing protected information about either tool.
PKI systems may use APIs to integrate with existing infrastructure, allowing simpler adoption and smoother deployment compared to replacing existing tools.
How PKIaaS Differs From On-Premise PKI
PKI-as-a-Service offers several distinct advantages over traditional on-premises PKI, primarily through its cloud-based architecture and managed service model. PKIaaS differentiates itself from private PKI in these ways:
| On-Premises PKI | PKI-as-a-Service | |
| Infrastructure Management | Requires on-prem hardware installations, ongoing maintenance, and self-managed software updates | No on-prem hardware or maintenance; provider handles software updates |
| Scalability | Limited by your physical infrastructure | Extensible and flexible to fluctuating demands and growth |
| Deployment Speed | Slow: weeks to several months | Rapid: pre-configured cloud environments launch in hours |
| Certificate Outage Prevention | Renewal tracking is time-consuming and complex, risking outages | Automated renewal and revocation provide simple, reliable outage prevention |
| Automation and Integration | Limited automations, custom scripting, and Application Programming Interface (API) compatibility | Ample automations and API support offer smooth customization and integration |
| Security and Compliance | Dependent on staff expertise, risking security breaches, compliance issues, and poor disaster recovery response | Security and compliance experts are part of your managed services, improving compliance with regulatory requirements, protection from data breaches, and disaster recovery assistance |
| Cost Structure | Significant initial investment (hardware, software, installation, training) and ongoing costs (maintenance, re-education) | Subscription-based pricing spreads costs over time, eliminating the need for large capital investments |
| Management Complexity | Requires specialized expertise, constant oversight, and regular maintenance, increasing costs and complexity | PKI service provider handles management, maintenance, security, and compliance for more visibility with less complexity |
Benefits of PKI-as-a-Service: The Move Away From On-Premise
Due to the numerous advantages of PKI-as-a-Service, businesses are increasingly transitioning from on-premises PKIs to PKIaaS.
Key benefits driving this shift include:
Cost Efficiency
PKIaaS operates on a subscription-based model, spreading costs over time and eliminating hefty upfront expenses of private PKI. This makes robust PKI accessible to businesses of all sizes.
Scalability
PKIaaS leverages cloud infrastructure for seamless scalability, allowing businesses to grow and adapt without limitations. Known as crypto agility, this elasticity ensures enterprises can scale their cryptographic key infrastructure without overcommitting resources.
Complete Visibility
PKI-as-a-Service providers offer total visibility into all issued certificates: full details, logs, expiration dates, and more. It’s both managed and automated, improving regulatory compliance while reducing the need for manual oversight.
Enhanced Security
PKIaaS providers adhere to strict enterprise security protocols, for highly effective threat protection. That means automated cryptographic key generation, digital signature protection, and reliable renewal and revocation for more comprehensive, stronger security.
Built-in Compliance
Many managed PKI services offer automated audit logging, which tracks every access decision for your digital certificates. By recording user identities, device posture, and risk factors, the service creates a detailed audit trail that meets compliance requirements without the need for manual reporting.
Simplified Management
PKI service providers handle all operational tasks. That includes key management, certificate authority functions, and compliance with industry standards. By offloading these functions to a managed provider, IT departments can focus on core business functions.
Rapid Deployment and Integration
In a recent survey, 50% of respondents cited infrastructure misconfigurations as a top security obstacle. PKIaaS uses preconfigured cloud environments designed to integrate smoothly with your existing infrastructure. You get reliable, near-instant deployment, enhancing security posture without extensive modifications.
Common Challenges with PKIaaS
Managed PKI services aren’t a magic solution to every problem. Be mindful of these risks and disadvantages:
- Incompatibility with Legacy PKI Infrastructure Management Practices: Moving from traditional PKI to PKI-as-a-Service isn’t just a system change — it’s a process change, too. Many enterprises and smaller organizations alike require operational updates, which can extend implementation.
- Unclear Responsibility: Along with procedural changes, implementing PKIaaS also requires a review of governance policies and ownership among teams. Who owns intra- and inter-departmental approvals? How will you enforce new policies? Who will enforce them? Don’t just define ownership — document it.
- Automation without Customization: PKIaaS platforms offer certificate automations that reduce manual work, minimize human errors, improve efficiency, and meet or exceed compliance requirements. However, you still need to personalize details like certificate lifetimes, trust policies, key sizes, and revocation practices to match company and industry standards.
In addition to your in-house PKI experts, lean on your PKIaaS provider to help streamline implementation, maximize personalization, and guide essential policy and governance updates.
When To Use PKI-as-a-Service
A managed PKIaaS solution may be right for your organization if you manage:
- Distributed Workforces: Across multiple facilities and remote teams, many organizations trust managed PKI services for secure network access.
- High Volumes of Digital Certificates: Managed PKI is perfect for organizations with an extensive number of certificates, which can require significant oversight.
- Rapid Certificate Issuance Needs: For teams needing to issue certificates on demand, PKIaaS can streamline the process without compromising compliance.
- Myriad Internet of Things (IoT) Devices: With hundreds, thousands, or even millions of IoT devices comes a need for individual device validation. At this scale, manual device management isn’t realistic, but PKI-as-a-Service can provide certificate security for IoT devices.
- Teams Without Sufficient PKI Experts: Without an appropriate number of specialized, highly trained staff members, you won’t have the resources to handle the complexities of traditional PKI in-house.
- Low-Budget Infrastructure: Traditional PKIs require expensive hardware and infrastructure: on-premise data centers, hardware security modules (HSMs) to store and manage keys, load balancers, maintenance staff, and more. PKIaaS solutions typically offer lower costs.
If you have plenty of PKI experts and just a few certificates, you can probably handle traditional PKI.
But for reliable, efficient, secure, and scalable PKI infrastructure — without the in-house headaches — PKI-as-a-Service is the ideal choice.
How To Migrate from Legacy PKI to PKIaaS
PKIaaS offers rapid deployment, but preparation is key. Follow this process for simplified implementation, onboarding, and long-term success.
Phase 1: Discover and Assess Details
Start with a discovery process to map out all PKI processes, along with current root CAs, issuing CAs, certificate profiles, and expiration dates. This is also the best time to identify and document all manual processes and unspoken policies, so include all teams in this phase.
Phase 2: Identify and Test Use Cases
Define the specific scenarios you want to test within the new PKI setup. To avoid major disruptions, choose low-risk certificate types and test simultaneously on both your legacy system and new platform.
Phase 3: Phased Rollout
When you’re ready to transition, be smart! This will be a gradual process. Issue new certificates through your new managed service while keeping legacy certificates on your legacy platform.
One by one, expired certificates will renew on your new platform until the transition is complete.
Phase 4: Maintenance
Once initial implementation, testing, and troubleshooting are all complete, increase automation and continuous monitoring processes to reduce (but not eliminate) manual oversight.
Automation can’t completely replace human inspection, nor should it. Over time, though, it should simplify the process. That’s especially true with managed services, where a team of PKI experts helps manage the workload.
Phase 5: Decommission Legacy PKI Infrastructure
When no legacy certificates remain, you can prepare to decommission your legacy PKI servers. While delicate, this final step improves security while reducing operational costs, so don’t skip it.
For more details on PKIaaS implementation, check out this article: Running PKI-as-a-Service.
The Industry Leader in PKI-as-a-Service: SecureW2’s Managed PKI
Transitioning from traditional on-premise PKI to a managed PKI solution can drastically enhance your organization’s security posture.
The SecureW2 JoinNow Platform is a comprehensive managed PKI-as-a-Service solution linked with our cloud-based RADIUS. It seamlessly integrates with your existing infrastructure for simple deployment with robust security capabilities.
Our managed PKIaaS solutions combine simplicity, security, and scalability to:
- Automate digital certificate issuance
- Strengthen authentication and authorization
- Protect sensitive data
- Enhance secure communications with advanced public key encryption
- Improve user experience
- Streamline certificate management
- Eliminate on-premise hardware
- Reduce operational costs
With features like automatic key generation, digital signatures, 802.1X authentication, and certificate authority functions, our PKI solutions are tailored to meet the demands of modern digital environments.
SecureW2 protects against man-in-the-middle attacks and unauthorized access, creating a highly secure and efficient public key infrastructure that protects your networks, users, devices, and data.
Ready to upgrade your security infrastructure? See how our managed PKI solution can transform your organization’s approach to security, simplify management, and save costs.
Take the first step toward a more secure, streamlined future. Request a free demo today.
Frequently Asked Questions
What is the PKI for DSC?
PKI for DSC (Digital Signing Certificate) is a certificate-based framework that proves a signer's identity and confirms a document hasn't been altered after signing. The signer's private key encrypts a hash of the document; any recipient can use the corresponding public key to verify both the signature and document integrity. DSCs carry legal weight under the ESIGN Act and UETA in the US and eIDAS in the EU. PKI-as-a service makes DSC issuance practical at scale: organizations can issue, manage, and revoke signing certificates through a cloud CA without standing up or maintaining on-premises infrastructure.
How does PKI work?
PKI works by using two cryptographic keys: a public key and a private key. The public key encrypts data or verifies digital signatures, while the private key decrypts data or creates digital signatures. This allows secure communication between trusted parties without ever transmitting sensitive credentials, such as passwords, over the network. Public keys are bound to a user, device, or application by certificates issues by a trusted Certificate Authority (CA).. When a connection is initiated, both parties present and validate their certificates to confirm their identities.
What is the purpose of PKI?
The purpose of PKI is to establish trusted digital identities and secure communications across networks, devices, applications, and users. PKI uses digital certificates and cryptographic key pairs to verify identities and encrypt sensitive data. Organizations commonly use PKI to enable secure Wi-Fi authentication, VPN access, HTTPS encryption, email security, device authentication, and passwordless access. Using PKI replaces vulnerable password-based authentication with certificate-based trust, reducing the risk of phishing, credential theft, and unauthorized access.
What are the two types of certificate authorities?
The two types of certificate authorities are the Root CA and the Intermediate CA. The Root CA sits at the top of the trust chain. It's self-signed, kept offline to protect its private key, and has a lifespan of roughly 25 years. Its trust is embedded directly in operating system and browser trust stores. The Intermediate CA, sometimes called an Issuing CA, operates below the root and issues end-entity certificates on its behalf. If an intermediate CA is compromised, it can be revoked without invalidating the root. This hierarchy is the backbone of how PKIaaS providers structure certificate issuance.
What are the three types of certificates?
The three core certificate types issued within a PKI are TLS/SSL certificates, code signing certificates, and client certificates. TLS/SSL certificates authenticate a server's identity and encrypt traffic between a browser and server. Code signing certificates verify a software publisher's identity and confirm that code hasn't been modified between build and distribution. Client certificates authenticate end users and devices — rather than passwords — to servers and network resources. In a PKI-as-a-service model, all three types are issued from the same managed CA hierarchy, giving organizations centralized visibility and control over every certificate across their environment.