Key Points
- Traditional network access control (NAC) network deployments and on-premises RADIUS servers use outdated password-based protocols; this vulnerability makes it hard to justify their complex implementation.
- Upgrading from password- to certificate-based authentication with a public key infrastructure (PKI) significantly strengthens NAC frameworks.
- JoinNow Cloud RADIUS and Dynamic PKI from SecureW2 provide a cloud-based NAC solution with real-time policy enforcement and certificate lifecycle automation.
NAC is an advanced cybersecurity measure that regulates which entities can gain access to specific network resources. Beyond traditional security parameters, NAC enforces specific access policies, so only compliant devices and authorized users gain network access, strengthening modern network architecture.
In this article, we’ll define NAC in detail, including architecture, various authentication methods, and a comparison against other network security measures. We’ll also explore best practices and step-by-step guidelines for effective NAC implementation within your existing IT infrastructure.
What Is Network Access Control?
Network access control (NAC) is a security framework that regulates how devices and users access network resources. NAC solutions function as gatekeepers that enforce predefined policies, ensuring only compliant, authorized devices and users gain access.
NAC relies on a combination of authentication, authorization, and endpoint compliance checks. It typically uses protocols including 802.1X and Remote Authentication Dial-In User Service (RADIUS) to verify user credentials and device identity before granting access.
NAC integrates with policy servers, a network access server (NAS), wireless access points, and other network components to create a comprehensive security architecture.
In most enterprise environments, NAC enforcement occurs at Layer 2 (the access layer), typically at the switch port or wireless access point using 802.1X port-based authentication. In this model, the supplicant (client device) communicates with an authenticator (switch or access point), which forwards authentication requests to an authentication server (usually a RADIUS server ). This ensures access decisions are made before a device is granted full network connectivity.
Through continuous monitoring and compliance enforcement, NAC avoids traditional network vulnerabilities, protecting sensitive data and critical resources from unauthorized access.
Capabilities of Network Access Control Solutions
NAC empowers organizations with:
- Network visibility: Monitor every device and user on your network, improving real-time visibility and enabling effective network management.
- Policy definition for devices and users: Define permissions, including guest access, for fine-tuned control over resources and actions.
- Authentication: Verify all device and user identities through credentials or digital certificates.
- Authorization: Grant limited access based on pre-defined policies specific to each user or device.
- Policy enforcement and lifecycle management: Manage access with real-time policy reviews and incident response.
- Security and compliance: Keep corporate networks secure — including wired and wireless networks, intranet, and virtual private networks (VPNs) — while complying with regulatory standards.
- Advanced integration: Implement NAC solutions without major infrastructure changes via native integrations or application programming interface (API).
How NAC Works
For robust and reliable security architecture, NAC best practices require detailed knowledge and a multi-faceted approach.
NAC Authentication Methods
Authentication is the first line of defense in NAC, making sure only verified users and devices gain access. Types of NAC authentication include:
- Certificate-based authentication: Utilizes PKI to authenticate devices and users via digital certificates .
- Password-based authentication: Relies on user-provided credentials, typically usernames and passwords. Though widely used, it’s considered less secure since bad actors can steal or guess passwords.
- Multi-factor authentication (MFA): Requires multiple forms of identification, such as a password and a biometric scan, significantly reducing the likelihood of unauthorized access.
- Biometric authentication: Uses unique biological characteristics like fingerprints, facial recognition, or retina scans for high-assurance authentication.
Authorization and Accounting in NAC
After authentication, NAC evaluates user or device access levels through:
- Authorization: Determines which resources a user or device can access based on predefined policies (user roles, device types, security posture).
- Accounting: Logs user activities to record resource access, ensuring security policy compliance and identifying potential security breaches.
Endpoint Compliance Checks
Endpoint compliance checks are integral to maintaining network integrity. Before a device gains full access, NAC:
- Checks that antivirus software is up to date
- Verifies necessary security patches
- Confirms proper configurations and settings
Network administrators may restrict or quarantine non-compliant devices until they meet requirements.
Remediation Processes in NAC
When a device fails compliance checks, NAC initiates remediation processes, which may include:
- Assisting users with installing required updates
- Applying necessary patches or configuring settings
- Re-running checks to determine compliance
Successfully remediated devices receive appropriate access.
VLANs for Network Segmentation
Virtual local area networks (VLANs) create isolated network segments separating devices by access level. For example, admins may place non-compliant devices into restricted VLANs to offer limited access while containing potential threats.
By limiting primary network traffic, segmentation improves security and optimizes network performance.
Types of Network Access Control
Each type of network access control plays a unique role in your broader security infrastructure.
Pre-Admission NAC
Pre-admission network control determines the security posture of endpoint devices before they’re allowed to connect, evaluating compliance standards such as up-to-date antivirus software and necessary patches.
Pre-admission control is the frontline defense against unauthorized access by unknown devices and users. It’s particularly useful for securing wireless networks and protecting remote access points.
Organizations typically enforce pre-admission NAC with 802.1X authentication before issuing IP addresses via dynamic host configuration protocol (DHCP) . This prevents rogue devices from joining the network at all.
Example: A company requires Wi-Fi-connected laptops to have updated antivirus definitions and critical operating system patches. A NAC solution checks these requirements for all access attempts. Non-compliant laptops are denied access, redirected to a remediation network, and prompted to install necessary updates before attempting to reconnect.
Post-Admission NAC
Post-admission NAC continuously monitors connected devices, reviewing real-time policies and dynamically adjusting access for enhanced security and compliance.
If a device falls out of compliance, modern post-admission NAC systems may use change of authorization (CoA) messages via RADIUS to dynamically control access, adjust VLAN assignments, or move the device to a quarantine network.
Example: An organization uses post-admission NAC to monitor devices on its internal network. A laptop that was compliant upon connection becomes infected with malware. The NAC detects the malware and automatically moves that laptop to a quarantine network, preventing infection on other devices while initiating secure remediation.
Role-based Access Control (RBAC)
RBAC assigns user permissions by title or role. Categorizing users into different roles (e.g., administrator, employee, guest) means each user can only access the resources necessary for their job duties. These tailored policies meet diverse organizational needs while ensuring compliance and preventing unauthorized access.
Example: In a hospital, staff members have varying levels of access to patient information. Doctors can access full patient records, including medical history, medications, and lab results. Nurses only have access to the information necessary to administer medication and take vital signs, while administrative staff can only access billing and scheduling information. With RBAC, the hospital grants staff the information they need for their jobs while protecting sensitive data.
Time-Based Access Control
Time-based access control (TBAC) restricts access based on predefined time windows, reducing the likelihood of unauthorized access while aligning network access control solutions with organizational security policies.
Example: A financial firm restricts trading system access for most employees to business hours (9 a.m. to 5 p.m.), significantly reducing the risk of unauthorized trading activities or breaches during off-hours. However, IT and security staff have 24/7 access to monitor and maintain system integrity.
Why NAC Is Important in Modern IT Environments
Modern organizations face an increasing risk of data breaches. With the growth of mobile devices and hybrid/remote work, network access control is essential to block unauthorized users and protect your information.
From enterprise Wi-Fi solutions to highly regulated healthcare and financial companies, many organizations deploy NAC solutions. They choose NAC for its distinct advantages: visibility, continuous trust, and reliable automation. But there are disadvantages to consider, too.
Advantages and Challenges of Network Access Control
NAC has distinct pros and cons for networks of all sizes. Here’s what to consider.
Advantages of NAC
NAC enables organizations to:
- Increase network visibility: Gain a centralized view of all connected devices and users.
- Improve cybersecurity: Strengthen protection with enhanced monitoring and faster response times.
- Reduce attack surface: Segment networks and access levels to limit exposure to security risks.
- Enforce continuous trust: Support continuous trust security with continuous monitoring and real-time policy enforcement.
- Save time: Automate authentication and authorization, block unauthorized access, and revoke non-compliant users and devices.
- Reduce costs: Lower IT and security expenses through automation, cloud infrastructure, and improved threat prevention.
- Enhance user experience: Enable faster, more reliable connections and maintain access with automated renewal for authorized users.
- Simplify control: Streamline access and lifecycle management across users, devices, and bring-your-own-device (BYOD) environments.
- Improve compliance: Maintain audit readiness and support regulatory compliance in highly regulated industries, such as healthcare, finance, and cybersecurity.
- Scale more easily: Support growth with flexible deployment across on-premises (on-prem), hybrid, and cloud environments.
Challenges of NAC
For as many benefits as NAC has, there are two key challenges to keep in mind:
- Complex implementation: Although cloud-based NAC is generally easier to deploy than on-prem solutions, all NAC environments are highly configurable. Achieving optimal setup and integration requires specialized expertise and a significant time investment.
- Ongoing maintenance: NAC effectiveness depends on up-to-date security policies, protocols, and compliance standards. From deployment through ongoing management, maintaining a secure NAC environment requires regular monitoring, updates, and administrative effort.
For a better end-to-end NAC experience, consider a managed provider like SecureW2.
Common Use Cases for NAC Solutions
Secure Corporate Wi-Fi With 802.1X Authentication
Many organizations secure enterprise wireless networks using NAC with 802.1X authentication. Instead of pre-shared keys, they use identity-based authentication backed by a RADIUS server.
When a device attempts to connect to a corporate service set identifier (SSID), NAC evaluates the user’s identity and the device’s credentials before granting access.
Based on policy rules, the system can:
- Dynamically assign VLANs
- Apply role-based access controls
- Restrict unmanaged devices
- Deny access entirely
For example, network administrators onboarding new employees can assign role-based access specific to each user and/or their managed devices. 802.1x authentication verifies these permissions and allows seamless, secure connections.
Learn how SecureW2 transformed AEBSD’s network security and streamlined student Wi-Fi access.
Enforce BYOD and Managed Device Policies
As organizations adopt BYOD policies, the distinction between corporate-managed and personal devices becomes increasingly important.
With NAC, IT teams can limit personal device access to approved applications, restrict unmanaged endpoints from sensitive internal systems, and automatically assign devices to segmented VLANs based on compliance status.
For example, a managed corporate laptop may receive full internal network access while a personal smartphone is limited to Wi-Fi or specific SaaS platforms. Universities are also implementing NAC to prevent unauthorized devices from accessing the network .
Control Headless and IoT Devices
Internet of Things (IoT) devices like printers, security cameras, medical devices, and other industrial systems may lack traditional authentication capabilities and can be difficult to patch regularly. The number of these devices is expanding rapidly, and an estimated 40.6 billion IoT devices will be connected to the internet by 2034 .
NAC improves IoT device control by profiling device types, segmenting networks, and limiting lateral communication between device categories.
For example, a doctor may need to connect new medical devices quickly without manual admin approval. Pre-authenticated devices streamline authentication, improve patient privacy, and block unauthorized use.
Manage Contractor and Guest Access
Organizations can use NAC to manage temporary access for contractors, vendors, and guests, granting restricted permissions without exposing sensitive resources.
NAC measures for temporary users may include time-based access controls, role-based restrictions, automated credential expiration, and isolation into guest VLANs.
For example, a NAC system may give a contractor project repository access while restricting financial systems access. When the contract ends, the NAC automatically revokes authorization.
Integrate NAC With VPN and Remote Access
NAC can extend beyond the LAN to hybrid and remote environments. Integrating NAC with VPN infrastructure allows organizations to:
- Authenticate users before tunnel establishment
- Verify device compliance before granting remote access
- Apply policy-based restrictions to remote sessions
For example, remote employees need secure access to your corporate networks. Adding NAC to your VPN helps authenticate and authorize remote access while keeping users, managed and unmanaged devices, and corporate data secure.
Support Regulated Industries and Ensure Compliance
Regulated industries must follow stringent protocols to comply with data privacy and protection regulations, including the Health Insurance Portability and Accountability Act (HIPAA), the General Data Protection Regulation (GDPR), and the Sarbanes-Oxley Act (SOX).
NAC solutions allow network administrators to define, automate, and enforce specific security policies.
For example, on a hospital network, doctors require full access to patient medical records. However, HIPAA doesn’t permit the same access to all hospital employees (e.g., marketing teams or receptionists). To stay compliant, hospitals must carefully control access to patient data on shared networks.
Enable Continuous Monitoring and Incident Response
Modern NAC solutions deliver in-depth insights and automated system controls for enhanced security. Many platforms provide continuous monitoring to track device behavior, policy compliance, and access patterns.
Centralized reporting provides visibility into:
- Every device attempting to authenticate
- Assigned roles and VLAN placement
- Policy enforcement decisions
- Compliance status changes
For example, if a device falls out of compliance while connected to the network, the NAC platform can trigger automatic remediation workflows to counter the threat. It may restrict the device to a quarantine VLAN, revoke privileges, or require re-authentication.
Components of NAC Cybersecurity Architecture
Robust network access control architecture requires integrating and synchronizing several critical components:
Policy Servers in NAC
Policy servers are like the brain of a NAC system, storing and managing access policies that govern which users and devices can access the network, which resources they can use, and under what conditions. The policy server evaluates these controls to make dynamic access decisions.
Network Access Servers
The network access server acts as the gatekeeper controlling entry. Upon receiving a connection request, the NAS communicates with the policy server to authenticate users and enforce security policies. This ensures only authorized, compliant devices and users connect to the network.
User and Device Identification Mechanisms
NAC systems require effective identification mechanisms such as credentials, digital certificates, or multi-factor authentication. Accurate identification allows the NAC to control access before entry and enforce appropriate access policies.
Network Admission Control
Network admission control is a subset of NAC that evaluates device health and compliance prior to access. Rigorous security posture checks, such as verifying antivirus updates and security patches, protect the network. Admins may quarantine or limit access for substandard devices until they receive necessary updates.
Quarantine and Guest Network Management
NAC systems use quarantine networks to isolate unsafe devices and mandate remediation steps. Guest network management provides temporary, restricted access for visitors without compromising sensitive internal resources. This dual approach maintains network integrity while accommodating diverse access needs.
RADIUS Integration With Network Access Control
NAC and RADIUS are both critical for managing network access, but they serve different purposes and offer distinct benefits.
What Is a RADIUS Server?
A RADIUS server is used for authenticating and authorizing users seeking wired or wireless network access. RADIUS centralizes authentication data and standardizes the process across the network. RADIUS integrates well with other network solutions, such as VPNs and Wi-Fi networks.
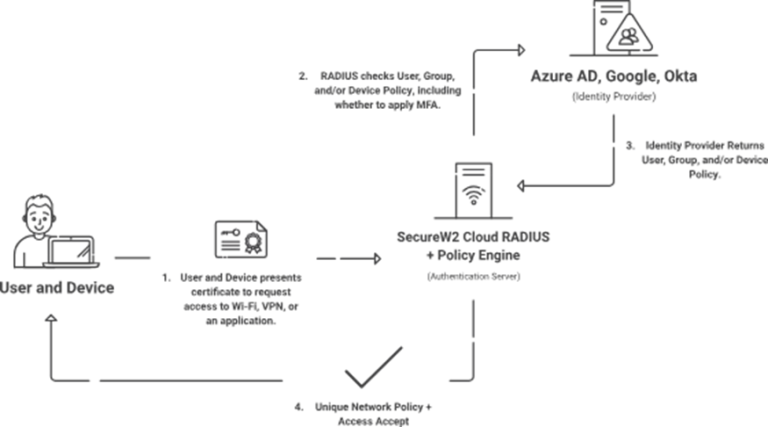
How Does RADIUS Fit Into a NAC Solution?
RADIUS seamlessly integrates into NAC architecture, acting as the authentication backbone to validate devices and users before granting access. The centralized RADIUS database enables efficient, consistent user verification across various access points, including wired, wireless, and VPN connections.
RADIUS supports Extensible Authentication Protocol (EAP) , an efficient means of certificate-based authentication to enhance endpoint compliance. NAC solutions can also use RADIUS to facilitate dynamic VLAN assignment, segmenting network traffic based on roles and compliance to maintain organizational security policies.
Adding RADIUS to NAC solutions creates a multi-layered security approach to mitigate risks and enforce security policies. The combination fortifies the security perimeter while enabling efficient access.
How to Choose a Network Access Control Software System
Modern NAC solutions should go beyond basic device profiling and password authentication. When evaluating a NAC platform, look for:
- Certificate-based authentication support
- Integration with identity providers (IdP) and mobile device management (MDM) platforms
- Dynamic policy enforcement
- Scalable RADIUS infrastructure
- Cloud compatibility and hybrid deployment support
- Automated remediation and lifecycle management
As networks become increasingly distributed and identity-centric, NAC solutions must seamlessly integrate with cloud identity systems and provide strong, phishing-resistant authentication.
On-Premises vs. Cloud-Based NAC
While NAC delivers significant advantages, organizations must weigh these against the challenges of implementation. The table below compares traditional NAC with modern cloud-based approaches:
| Aspect | Traditional On-Premises NAC | Modern Cloud-Based NAC |
|---|---|---|
| Deployment | Requires dedicated servers/appliances, complex setup, and high availability configuration | Cloud-managed; quick deployment with minimal on-site infrastructure |
| Authentication | Often relies on password-based protocols (e.g., PEAP-MSCHAPv2) | Certificate-based (EAP-TLS) with PKI; phishing-resistant and passwordless |
| Scalability | Limited by hardware; scaling requires additional servers and maintenance | Highly scalable; handles growth, remote users, and hybrid environments easily |
| Management & Maintenance | High operational burden (patching, updates, redundancy) | Provider-managed; automatic updates and built-in redundancy |
| Security | Vulnerable to credential theft, MITM if client cert validation is weak; static policies | Stronger mutual authentication, dynamic policy enforcement, continuous monitoring |
| Cost Structure | High upfront hardware/software costs + ongoing maintenance | Subscription-based; lower total cost of ownership for most organizations |
| Integration | Tighter coupling with legacy directories; more custom work | Seamless with modern IdPs (Okta, Entra ID, etc.), MDM, and device Trust tools |
| Best For | Environments needing full data control on-prem | Hybrid/remote workforces, BYOD, IoT, and organizations prioritizing ease and agility |
6 Best Practices to Implement a NAC Network
Follow these best practices when adding NAC to your security environment.
- Log all devices: Survey and document all endpoint devices, including company-owned remote employee devices, workers’ own devices, and IoT devices.
- Categorize all users: Reference org charts and network directories to create a comprehensive log of everyone who needs access.
- Create a network access control list: Segment access rules and permitted actions by department, title, and/or employment type (full-time, part-time, temporary, contractor, guest).
- Implement role-based access control: Enforce least-privilege access, only allowing users/devices to access resources required to perform their duties.
- Employ multi-factor authentication: Strengthen network security by requiring MFA, especially for environments relying on traditional credentials.
- Educate your support staff: Provide training and resources to empower your team to effectively manage and maintain your NAC environment.
See our NAC best practices for more detail.
JoinNow Cloud RADIUS and JoinNow NetAuth Enhance Network Access Control
The SecureW2 Cloud RADIUS platform enhances network security through robust authentication and reliable access management.
We simplify network access control with a scalable, cloud-based RADIUS server that easily integrates with your existing network infrastructure. Our self-service portal simplifies setup, management, and enforcement.
Unlike traditional RADIUS servers, Cloud RADIUS uses certificate-based authentication, restricting access to only users and devices with active authorization.
SecureW2 agentless 802.1x technology enforces network access control with rules from integrated providers — including Okta, Entra ID, Jamf, and CrowdStrike — limiting access to devices and users with rigorous security standards.
Our certificate lifecycle management solution works with your cloud identity environment, automating certificate enrollment and revocation based on real-time policy updates while avoiding certificate outages.
With Cloud RADIUS, it’s easier than ever to manage digital certificates and improve network security. Schedule a free demo to learn more.
Frequently Asked Questions
What Is the Purpose of NAC?
The primary purpose of network access control (NAC) is to ensure that only authenticated, authorized, and policy-compliant users and devices can access network resources.
What Problems Does Network Access Control Address?
With hybrid and remote workforces, more mobile and IoT devices, and varied network environments, cyber threat prevention grows increasingly more difficult.
NAC helps organizations automate, streamline, and improve security across corporate networks. Through rigorous authentication and authorization protocols, strict security policies, and user- and device-specific permissions, NAC protects your organization and its data.
How Does Network Access Control Work With Continuous-Trust Network Access?
The best NAC provides continuous trust by authenticating end entities in real time, automatically revoking access when users or devices lose authorization or fall out of compliance.
To follow continuous-trust or zero-trust network access (ZTNA) policies, ensure your NAC provider enforces access based on live signals (not static tokens) across all your other security tools, including IdP, MDM, and XDR. Without rapid incident response and instant revocation, it’s not true zero-trust security.
What Is the Difference Between a Firewall and NAC?
Firewalls typically enforce traffic policies at the network perimeter or segmentation boundaries. NAC enforces device-level access at the point of authentication, placing greater emphasis on internal security and compliance.
What Is the Difference Between NAC and VPN?
NAC and VPN servers fulfill complementary roles in network security.
A VPN creates an encrypted tunnel between a remote device and a public network, creating a secure connection to protect data transmissions.
NAC governs network access, determining which devices gain access and their specific access restrictions.
VPN connections often apply NAC policies to enforce authentication and compliance requirements for remote users.
What Are the Best NAC Solutions?
The best NAC solution depends on an organization’s architecture, scale, and security requirements.
Leading enterprise NAC platforms generally offer deep integration with switching and wireless infrastructure, identity providers, and endpoint management systems. They operate with certificate-based authentication, automated lifecycle management, and dynamic policy enforcement at scale.
When evaluating options, organizations should focus less on brand rankings and more on architectural fit.